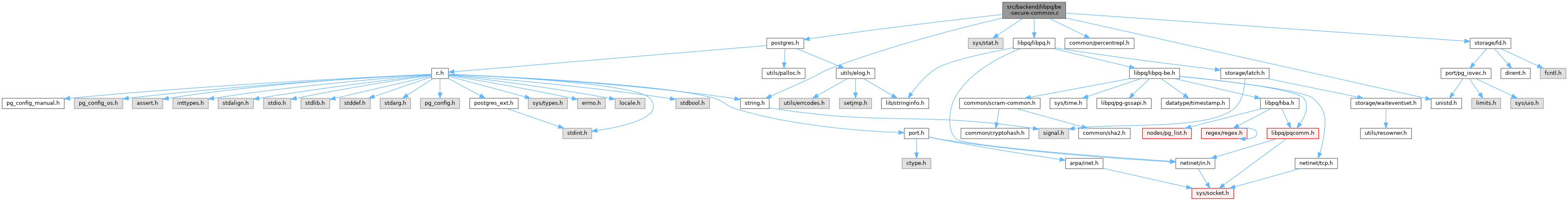
#include "postgres.h"
#include <sys/stat.h>
#include <unistd.h>
#include "common/percentrepl.h"
#include "common/string.h"
#include "libpq/libpq.h"
#include "storage/fd.h"
#include "utils/builtins.h"
#include "utils/guc.h"
Go to the source code of this file.
◆ check_ssl_key_file_permissions()
| bool check_ssl_key_file_permissions |
( |
const char * |
ssl_key_file, |
|
|
bool |
isServerStart |
|
) |
| |
Definition at line 121 of file be-secure-common.c.
122{
125
127 {
130 errmsg(
"could not access private key file \"%s\": %m",
132 return false;
133 }
134
135
137 {
140 errmsg(
"private key file \"%s\" is not a regular file",
142 return false;
143 }
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161#if !defined(WIN32) && !defined(__CYGWIN__)
163 {
166 errmsg(
"private key file \"%s\" must be owned by the database user or root",
168 return false;
169 }
170
173 {
176 errmsg(
"private key file \"%s\" has group or world access",
178 errdetail(
"File must have permissions u=rw (0600) or less if owned by the database user, or permissions u=rw,g=r (0640) or less if owned by root.")));
179 return false;
180 }
181#endif
182
183 return true;
184}
int errcode_for_file_access(void)
int errcode(int sqlerrcode)
int errdetail(const char *fmt,...) pg_attribute_printf(1
#define ereport(elevel,...)
static char buf[DEFAULT_XLOG_SEG_SIZE]
References buf, ereport, errcode(), errcode_for_file_access(), errdetail(), errmsg, FATAL, fb(), LOG, S_IRWXG, S_IRWXO, S_ISREG, S_IWGRP, S_IXGRP, ssl_key_file, and stat.
Referenced by init_host_context().
◆ load_hosts()
Definition at line 365 of file be-secure-common.c.
366{
373
374
375
376
377
379 {
380 if (err_msg)
381 *err_msg =
psprintf(
"cannot load config from \"%s\", return variable missing",
384 }
386
387
388
389
390
391
392
395 {
398
400 }
401
403
405 {
407
408
409
410
411
414 {
416 continue;
417 }
418
420 }
421
422
425
427 {
428 if (err_msg)
429 *err_msg =
psprintf(
"loading config from \"%s\" failed due to parsing error",
432 }
433
436
438}
static HostsLine * parse_hosts_line(TokenizedAuthLine *tok_line, int elevel)
void free_auth_file(FILE *file, int depth)
void tokenize_auth_file(const char *filename, FILE *file, List **tok_lines, int elevel, int depth)
FILE * open_auth_file(const char *filename, int elevel, int depth, char **err_msg)
List * lappend(List *list, void *datum)
char * psprintf(const char *fmt,...)
References fb(), free_auth_file(), HOSTSFILE_EMPTY, HOSTSFILE_LOAD_FAILED, HOSTSFILE_LOAD_OK, HOSTSFILE_MISSING, HostsFileName, lappend(), lfirst, LOG, newline, NIL, open_auth_file(), parse_hosts_line(), psprintf(), and tokenize_auth_file().
Referenced by be_tls_init().
◆ parse_hosts_line()
Definition at line 195 of file be-secure-common.c.
196{
201
207
208
211
212
216 {
217 if ((
tokens->length > 1) &&
219 {
222 errmsg(
"default and non-SNI entries cannot be mixed with other entries"),
223 errcontext(
"line %d of configuration file \"%s\"",
226 }
227
229 }
230
231
233 if (!field)
234 {
237 errmsg(
"missing entry at end of line"),
238 errcontext(
"line %d of configuration file \"%s\"",
241 }
244 {
247 errmsg(
"multiple values specified for SSL certificate"),
248 errcontext(
"line %d of configuration file \"%s\"",
251 }
254
255
257 if (!field)
258 {
261 errmsg(
"missing entry at end of line"),
262 errcontext(
"line %d of configuration file \"%s\"",
265 }
268 {
271 errmsg(
"multiple values specified for SSL key"),
272 errcontext(
"line %d of configuration file \"%s\"",
275 }
278
279
281 if (!field)
285 {
288 errmsg(
"multiple values specified for SSL CA"),
289 errcontext(
"line %d of configuration file \"%s\"",
292 }
295
296
298 if (field)
299 {
302 {
305 errmsg(
"multiple values specified for SSL passphrase command"),
306 errcontext(
"line %d of configuration file \"%s\"",
309 }
312
313
314
315
316
317
319 if (field)
320 {
323
324
325
326
327
328
330 {
333 errmsg(
"extra fields at end of line"),
334 errcontext(
"line %d of configuration file \"%s\"",
337 }
338
340 {
343 errmsg(
"incorrect syntax for boolean value SSL_passphrase_cmd_reload"),
344 errcontext(
"line %d of configuration file \"%s\"",
347 }
348 }
349 }
350
352}
bool parse_bool(const char *value, bool *result)
char * pstrdup(const char *in)
void * palloc0(Size size)
#define foreach_ptr(type, var, lst)
static ListCell * list_head(const List *l)
static ListCell * lnext(const List *l, const ListCell *c)
References ereport, errcode(), errcontext, errmsg, fb(), foreach_ptr, hostname, lappend(), lfirst, linitial, list_head(), lnext(), NIL, palloc0(), parse_bool(), pstrdup(), and token.
Referenced by load_hosts().
◆ run_ssl_passphrase_command()
Definition at line 46 of file be-secure-common.c.
48{
50 char *command;
54
58
60
63 {
66 errmsg(
"could not execute command \"%s\": %m",
67 command)));
69 }
70
72 {
74 {
78 errmsg(
"could not read from command \"%s\": %m",
79 command)));
81 }
82 }
83
86 {
90 errmsg(
"could not close pipe to external command: %m")));
92 }
94 {
95 char *reason;
96
101 errmsg(
"command \"%s\" failed",
102 command),
106 }
107
108
110
114}
#define Assert(condition)
int int errdetail_internal(const char *fmt,...) pg_attribute_printf(1
FILE * OpenPipeStream(const char *command, const char *mode)
int ClosePipeStream(FILE *file)
void pfree(void *pointer)
char * replace_percent_placeholders(const char *instr, const char *param_name, const char *letters,...)
void explicit_bzero(void *buf, size_t len)
int pg_strip_crlf(char *str)
char * wait_result_to_str(int exitstatus)
References Assert, buf, ClosePipeStream(), ereport, errcode_for_file_access(), errdetail_internal(), errmsg, ERROR, error(), explicit_bzero(), fb(), len, LOG, OpenPipeStream(), pfree(), pg_strip_crlf(), replace_percent_placeholders(), and wait_result_to_str().
Referenced by ssl_external_passwd_cb().