#include "postgres.h"#include <signal.h>#include <fcntl.h>#include <ctype.h>#include <sys/socket.h>#include <netdb.h>#include <netinet/in.h>#include <netinet/tcp.h>#include <arpa/inet.h>#include "libpq/libpq.h"#include "miscadmin.h"#include "storage/latch.h"#include "tcop/tcopprot.h"#include "utils/injection_point.h"#include "utils/wait_event.h"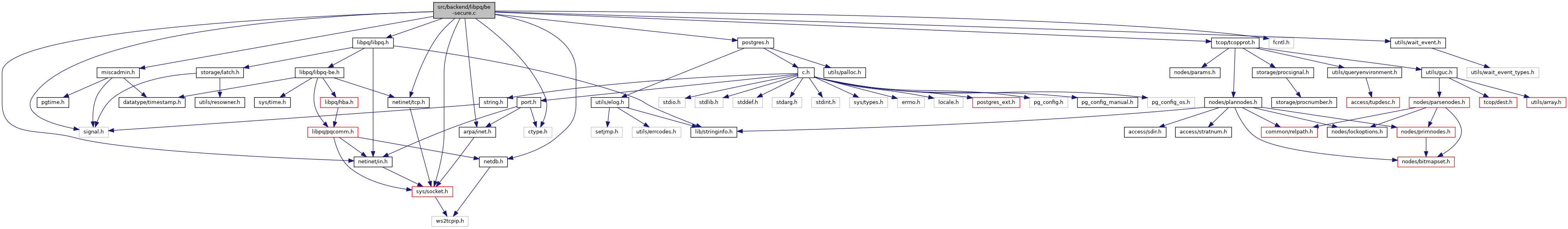
Go to the source code of this file.
Functions | |
| int | secure_initialize (bool isServerStart) |
| void | secure_destroy (void) |
| bool | secure_loaded_verify_locations (void) |
| int | secure_open_server (Port *port) |
| void | secure_close (Port *port) |
| ssize_t | secure_read (Port *port, void *ptr, size_t len) |
| ssize_t | secure_raw_read (Port *port, void *ptr, size_t len) |
| ssize_t | secure_write (Port *port, const void *ptr, size_t len) |
| ssize_t | secure_raw_write (Port *port, const void *ptr, size_t len) |
Function Documentation
◆ secure_close()
Definition at line 171 of file be-secure.c.
References be_tls_close(), and port.
Referenced by socket_close().
◆ secure_destroy()
Definition at line 92 of file be-secure.c.
References be_tls_destroy().
Referenced by process_pm_reload_request().
◆ secure_initialize()
Definition at line 79 of file be-secure.c.
References be_tls_init(), and fb().
Referenced by BackendMain(), PostmasterMain(), and process_pm_reload_request().
◆ secure_loaded_verify_locations()
Definition at line 103 of file be-secure.c.
References fb().
Referenced by ClientAuthentication().
◆ secure_open_server()
Definition at line 116 of file be-secure.c.
References Assert, be_tls_open_server(), buf, DEBUG2, elog, ereport, errmsg_internal(), fb(), INJECTION_POINT, len, LOG, palloc(), pfree(), port, pq_buffer_remaining_data(), pq_endmsgread(), pq_getbytes(), pq_startmsgread(), and STATUS_ERROR.
Referenced by ProcessSSLStartup(), and ProcessStartupPacket().
◆ secure_raw_read()
Definition at line 272 of file be-secure.c.
References Assert, fb(), len, memcpy(), pgwin32_noblock, port, and recv.
Referenced by be_gssapi_read(), port_bio_read(), read_or_wait(), and secure_read().
◆ secure_raw_write()
Definition at line 381 of file be-secure.c.
References fb(), len, pgwin32_noblock, port, and send.
Referenced by be_gssapi_write(), port_bio_write(), secure_open_gssapi(), and secure_write().
◆ secure_read()
Definition at line 183 of file be-secure.c.
References Assert, be_gssapi_read(), be_tls_read(), EAGAIN, ereport, errcode(), errmsg, WaitEvent::events, EWOULDBLOCK, FATAL, fb(), FeBeWaitSet, FeBeWaitSetSocketPos, len, ModifyWaitEvent(), MyLatch, port, ProcessClientReadInterrupt(), ResetLatch(), secure_raw_read(), WaitEventSetWait(), WL_LATCH_SET, WL_POSTMASTER_DEATH, and WL_SOCKET_READABLE.
Referenced by pq_getbyte_if_available(), and pq_recvbuf().
◆ secure_write()
Definition at line 309 of file be-secure.c.
References Assert, be_gssapi_write(), be_tls_write(), EAGAIN, ereport, errcode(), errmsg, WaitEvent::events, EWOULDBLOCK, FATAL, fb(), FeBeWaitSet, FeBeWaitSetSocketPos, len, ModifyWaitEvent(), MyLatch, port, ProcessClientWriteInterrupt(), ResetLatch(), secure_raw_write(), WaitEventSetWait(), WL_LATCH_SET, WL_POSTMASTER_DEATH, and WL_SOCKET_WRITEABLE.
Referenced by internal_flush_buffer(), and ProcessStartupPacket().
Variable Documentation
◆ ssl_ca_file
| char* ssl_ca_file |
Definition at line 40 of file be-secure.c.
Referenced by be_tls_init().
◆ ssl_cert_file
| char* ssl_cert_file |
Definition at line 38 of file be-secure.c.
Referenced by be_tls_init().
◆ ssl_crl_dir
| char* ssl_crl_dir |
Definition at line 42 of file be-secure.c.
Referenced by init_host_context().
◆ ssl_crl_file
| char* ssl_crl_file |
Definition at line 41 of file be-secure.c.
Referenced by init_host_context().
◆ ssl_dh_params_file
| char* ssl_dh_params_file |
Definition at line 43 of file be-secure.c.
Referenced by initialize_dh().
◆ ssl_key_file
| char* ssl_key_file |
Definition at line 39 of file be-secure.c.
Referenced by be_tls_init(), and check_ssl_key_file_permissions().
◆ ssl_library
| char* ssl_library |
Definition at line 37 of file be-secure.c.
◆ ssl_max_protocol_version
| int ssl_max_protocol_version = PG_TLS_ANY |
Definition at line 62 of file be-secure.c.
Referenced by be_tls_init(), and be_tls_open_server().
◆ ssl_min_protocol_version
| int ssl_min_protocol_version = PG_TLS1_2_VERSION |
Definition at line 61 of file be-secure.c.
Referenced by be_tls_init(), and be_tls_open_server().
◆ ssl_passphrase_command
| char* ssl_passphrase_command |
Definition at line 44 of file be-secure.c.
Referenced by be_tls_init(), default_openssl_tls_init(), and set_rot13().
◆ ssl_passphrase_command_supports_reload
| bool ssl_passphrase_command_supports_reload |
Definition at line 45 of file be-secure.c.
Referenced by be_tls_init(), and default_openssl_tls_init().
◆ ssl_sni
Definition at line 65 of file be-secure.c.
Referenced by be_tls_init(), and init_host_context().
◆ SSLCipherList
Definition at line 53 of file be-secure.c.
Referenced by be_tls_init().
◆ SSLCipherSuites
Definition at line 52 of file be-secure.c.
Referenced by be_tls_init().
◆ SSLECDHCurve
| char* SSLECDHCurve |
Definition at line 56 of file be-secure.c.
Referenced by initialize_ecdh().
◆ SSLPreferServerCiphers
| bool SSLPreferServerCiphers |
Definition at line 59 of file be-secure.c.
Referenced by be_tls_init().