#include "postgres.h"#include <unistd.h>#include "libpq/auth.h"#include "libpq/be-gssapi-common.h"#include "libpq/libpq.h"#include "miscadmin.h"#include "pgstat.h"#include "port/pg_bswap.h"#include "storage/latch.h"#include "utils/injection_point.h"#include "utils/memutils.h"#include "utils/wait_event.h"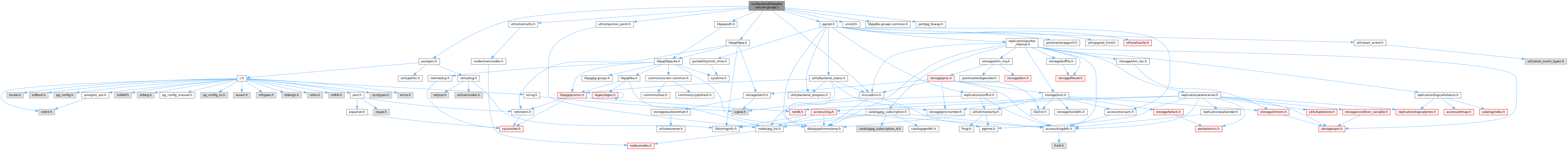
Go to the source code of this file.
Macros | |
| #define | PQ_GSS_MAX_PACKET_SIZE 16384 /* includes uint32 header word */ |
| #define | PQ_GSS_AUTH_BUFFER_SIZE 65536 /* includes uint32 header word */ |
Functions | |
| ssize_t | be_gssapi_write (Port *port, const void *ptr, size_t len) |
| ssize_t | be_gssapi_read (Port *port, void *ptr, size_t len) |
| static ssize_t | read_or_wait (Port *port, ssize_t len) |
| ssize_t | secure_open_gssapi (Port *port) |
| bool | be_gssapi_get_auth (Port *port) |
| bool | be_gssapi_get_enc (Port *port) |
| const char * | be_gssapi_get_princ (Port *port) |
| bool | be_gssapi_get_delegation (Port *port) |
Macro Definition Documentation
◆ PQ_GSS_AUTH_BUFFER_SIZE
Definition at line 62 of file be-secure-gssapi.c.
◆ PQ_GSS_MAX_PACKET_SIZE
Definition at line 54 of file be-secure-gssapi.c.
Function Documentation
◆ be_gssapi_get_auth()
Definition at line 746 of file be-secure-gssapi.c.
References port.
Referenced by PerformAuthentication(), and pgstat_bestart_security().
◆ be_gssapi_get_delegation()
Definition at line 784 of file be-secure-gssapi.c.
References port.
Referenced by check_conn_params(), dblink_connstr_check(), dblink_security_check(), PerformAuthentication(), pgfdw_security_check(), and pgstat_bestart_security().
◆ be_gssapi_get_enc()
Definition at line 758 of file be-secure-gssapi.c.
References port.
Referenced by PerformAuthentication(), and pgstat_bestart_security().
◆ be_gssapi_get_princ()
Definition at line 771 of file be-secure-gssapi.c.
Referenced by PerformAuthentication(), and pgstat_bestart_security().
◆ be_gssapi_read()
Definition at line 272 of file be-secure-gssapi.c.
References _, Assert, COMMERROR, ECONNRESET, ereport, errmsg, EWOULDBLOCK, fb(), input, len, memcpy(), Min, output, pg_GSS_error(), pg_ntoh32, port, PQ_GSS_MAX_PACKET_SIZE, PqGSSRecvBuffer, PqGSSRecvLength, PqGSSResultBuffer, PqGSSResultLength, PqGSSResultNext, and secure_raw_read().
Referenced by secure_read().
◆ be_gssapi_write()
Definition at line 105 of file be-secure-gssapi.c.
References _, Assert, COMMERROR, ECONNRESET, elog, ereport, errmsg, fb(), input, len, memcpy(), output, pg_GSS_error(), pg_hton32, port, PQ_GSS_MAX_PACKET_SIZE, PqGSSMaxPktSize, PqGSSSendBuffer, PqGSSSendConsumed, PqGSSSendLength, PqGSSSendNext, and secure_raw_write().
Referenced by secure_write().
◆ read_or_wait()
Definition at line 433 of file be-secure-gssapi.c.
References EAGAIN, EINTR, EWOULDBLOCK, fb(), len, port, PqGSSRecvBuffer, PqGSSRecvLength, secure_raw_read(), WaitLatchOrSocket(), WL_EXIT_ON_PM_DEATH, and WL_SOCKET_READABLE.
Referenced by secure_open_gssapi().
◆ secure_open_gssapi()
Definition at line 505 of file be-secure-gssapi.c.
References _, COMMERROR, EAGAIN, EINTR, ereport, errcode(), errmsg, EWOULDBLOCK, FATAL, fb(), free, INJECTION_POINT, input, malloc, memcpy(), MemoryContextAllocZero(), output, pg_gss_accept_delegation, pg_GSS_error(), pg_hton32, pg_krb_server_keyfile, pg_ntoh32, pg_store_delegated_credential(), port, PQ_GSS_AUTH_BUFFER_SIZE, PQ_GSS_MAX_PACKET_SIZE, PqGSSMaxPktSize, PqGSSRecvBuffer, PqGSSRecvLength, PqGSSResultBuffer, PqGSSResultLength, PqGSSResultNext, PqGSSSendBuffer, PqGSSSendConsumed, PqGSSSendLength, PqGSSSendNext, read_or_wait(), secure_raw_write(), setenv, TopMemoryContext, WaitLatchOrSocket(), WL_EXIT_ON_PM_DEATH, and WL_SOCKET_WRITEABLE.
Referenced by ProcessStartupPacket().
Variable Documentation
◆ PqGSSMaxPktSize
|
static |
Definition at line 84 of file be-secure-gssapi.c.
Referenced by be_gssapi_write(), and secure_open_gssapi().
◆ PqGSSRecvBuffer
|
static |
Definition at line 76 of file be-secure-gssapi.c.
Referenced by be_gssapi_read(), read_or_wait(), and secure_open_gssapi().
◆ PqGSSRecvLength
|
static |
Definition at line 77 of file be-secure-gssapi.c.
Referenced by be_gssapi_read(), read_or_wait(), and secure_open_gssapi().
◆ PqGSSResultBuffer
|
static |
Definition at line 79 of file be-secure-gssapi.c.
Referenced by be_gssapi_read(), and secure_open_gssapi().
◆ PqGSSResultLength
|
static |
Definition at line 80 of file be-secure-gssapi.c.
Referenced by be_gssapi_read(), and secure_open_gssapi().
◆ PqGSSResultNext
|
static |
Definition at line 81 of file be-secure-gssapi.c.
Referenced by be_gssapi_read(), and secure_open_gssapi().
◆ PqGSSSendBuffer
|
static |
Definition at line 69 of file be-secure-gssapi.c.
Referenced by be_gssapi_write(), and secure_open_gssapi().
◆ PqGSSSendConsumed
|
static |
Definition at line 73 of file be-secure-gssapi.c.
Referenced by be_gssapi_write(), and secure_open_gssapi().
◆ PqGSSSendLength
|
static |
Definition at line 70 of file be-secure-gssapi.c.
Referenced by be_gssapi_write(), and secure_open_gssapi().
◆ PqGSSSendNext
|
static |
Definition at line 71 of file be-secure-gssapi.c.
Referenced by be_gssapi_write(), and secure_open_gssapi().