#include "postgres.h"#include <sys/param.h>#include <sys/select.h>#include <sys/socket.h>#include <netinet/in.h>#include <netdb.h>#include <pwd.h>#include <unistd.h>#include "commands/user.h"#include "common/ip.h"#include "common/md5.h"#include "libpq/auth.h"#include "libpq/crypt.h"#include "libpq/libpq.h"#include "libpq/oauth.h"#include "libpq/pqformat.h"#include "libpq/sasl.h"#include "libpq/scram.h"#include "miscadmin.h"#include "port/pg_bswap.h"#include "postmaster/postmaster.h"#include "replication/walsender.h"#include "storage/ipc.h"#include "tcop/backend_startup.h"#include "utils/memutils.h"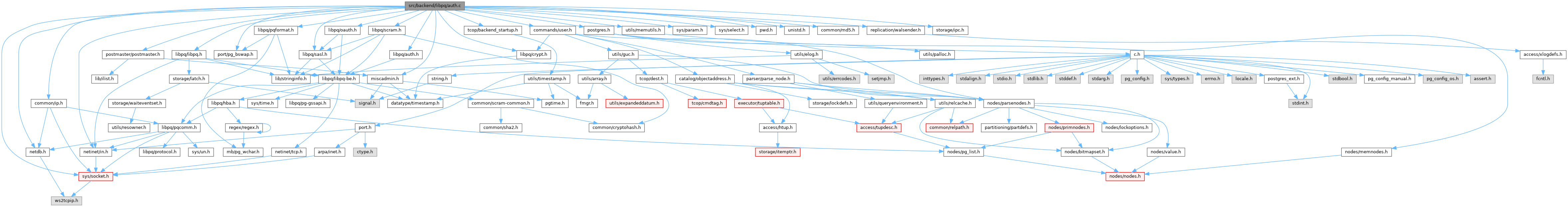
Go to the source code of this file.
Macros | |
| #define | IDENT_USERNAME_MAX 512 |
| #define | IDENT_PORT 113 |
| #define | HOSTNAME_LOOKUP_DETAIL(port) |
Functions | |
| static void | auth_failed (Port *port, int elevel, int status, const char *logdetail) |
| static char * | recv_password_packet (Port *port) |
| static int | CheckPasswordAuth (Port *port, const char **logdetail) |
| static int | CheckPWChallengeAuth (Port *port, const char **logdetail) |
| static int | CheckMD5Auth (Port *port, char *shadow_pass, const char **logdetail) |
| static int | ident_inet (Port *port) |
| static int | auth_peer (Port *port) |
| void | set_authn_id (Port *port, const char *id) |
| void | ClientAuthentication (Port *port) |
| void | sendAuthRequest (Port *port, AuthRequest areq, const void *extradata, int extralen) |
| static bool | is_ident_whitespace (const char c) |
| static bool | interpret_ident_response (const char *ident_response, char *ident_user) |
Variables | |
| char * | pg_krb_server_keyfile |
| bool | pg_krb_caseins_users |
| bool | pg_gss_accept_delegation |
| ClientAuthentication_hook_type | ClientAuthentication_hook = NULL |
Macro Definition Documentation
◆ HOSTNAME_LOOKUP_DETAIL
◆ IDENT_PORT
◆ IDENT_USERNAME_MAX
Function Documentation
◆ auth_failed()
Definition at line 234 of file auth.c.
References _, Assert, ereport, errcode(), ERRCODE_INVALID_PASSWORD, errdetail_log(), errmsg, FATAL, fb(), gettext_noop, pg_unreachable, port, proc_exit(), psprintf(), STATUS_EOF, uaBSD, uaCert, uaGSS, uaIdent, uaImplicitReject, uaLDAP, uaMD5, uaOAuth, uaPAM, uaPassword, uaPeer, uaReject, uaSCRAM, uaSSPI, and uaTrust.
Referenced by ClientAuthentication().
◆ auth_peer()
Definition at line 1870 of file auth.c.
References Assert, ClientConnectionInfo::authn_id, buf, check_usermap(), ereport, errcode(), errcode_for_socket_access(), errmsg, fb(), getpeereid(), LOG, MyClientConnectionInfo, port, set_authn_id(), and STATUS_ERROR.
Referenced by ClientAuthentication().
◆ CheckMD5Auth()
Definition at line 888 of file auth.c.
References AUTH_REQ_MD5, ereport, errmsg, fb(), LOG, md5_crypt_verify(), pfree(), pg_strong_random(), port, recv_password_packet(), result, sendAuthRequest(), STATUS_EOF, and STATUS_ERROR.
Referenced by CheckPWChallengeAuth().
◆ CheckPasswordAuth()
Definition at line 793 of file auth.c.
References AUTH_REQ_PASSWORD, fb(), get_role_password(), pfree(), plain_crypt_verify(), port, recv_password_packet(), result, sendAuthRequest(), set_authn_id(), STATUS_EOF, STATUS_ERROR, and STATUS_OK.
Referenced by ClientAuthentication().
◆ CheckPWChallengeAuth()
Definition at line 828 of file auth.c.
References Assert, CheckMD5Auth(), CheckSASLAuth(), fb(), get_password_type(), get_role_password(), Password_encryption, PASSWORD_TYPE_MD5, pfree(), pg_be_scram_mech, port, set_authn_id(), STATUS_OK, uaMD5, and uaSCRAM.
Referenced by ClientAuthentication().
◆ ClientAuthentication()
Definition at line 374 of file auth.c.
References _, am_db_walsender, am_walsender, Assert, auth_failed(), auth_peer(), AUTH_REQ_GSS, AUTH_REQ_OK, AUTH_REQ_SSPI, ClientConnectionInfo::authn_id, CHECK_FOR_INTERRUPTS, CheckPasswordAuth(), CheckPWChallengeAuth(), CheckSASLAuth(), ClientAuthentication_hook, clientCertFull, clientCertOff, ereport, errcode(), errmsg, FATAL, FATAL_CLIENT_ONLY, fb(), hba_authname(), hba_getauthmethod(), HOSTNAME_LOOKUP_DETAIL, ident_inet(), LOG, LOG_CONNECTION_AUTHENTICATION, log_connections, MemoryContextAllocZero(), MyClientConnectionInfo, pg_be_oauth_mech, pg_getnameinfo_all(), port, secure_loaded_verify_locations(), sendAuthRequest(), STATUS_ERROR, STATUS_OK, TopMemoryContext, uaBSD, uaCert, uaGSS, uaIdent, uaImplicitReject, uaLDAP, uaMD5, uaOAuth, uaPAM, uaPassword, uaPeer, uaReject, uaSCRAM, uaSSPI, and uaTrust.
Referenced by PerformAuthentication().
◆ ident_inet()
Definition at line 1685 of file auth.c.
References bind, CHECK_FOR_INTERRUPTS, check_usermap(), closesocket, connect, EINTR, ereport, errcode_for_socket_access(), errmsg, fb(), IDENT_PORT, IDENT_USERNAME_MAX, interpret_ident_response(), LOG, pg_freeaddrinfo_all(), pg_getaddrinfo_all(), pg_getnameinfo_all(), PGINVALID_SOCKET, port, recv, send, set_authn_id(), snprintf, socket, and STATUS_ERROR.
Referenced by ClientAuthentication().
◆ interpret_ident_response()
Definition at line 1604 of file auth.c.
References fb(), i, IDENT_USERNAME_MAX, and is_ident_whitespace().
Referenced by ident_inet().
◆ is_ident_whitespace()
Definition at line 1592 of file auth.c.
Referenced by interpret_ident_response().
◆ recv_password_packet()
Definition at line 712 of file auth.c.
References buf, DEBUG5, elog, ereport, errcode(), ERRCODE_INVALID_PASSWORD, ERRCODE_PROTOCOL_VIOLATION, errmsg, ERROR, fb(), initStringInfo(), pfree(), PG_MAX_AUTH_TOKEN_LENGTH, pq_getbyte(), pq_getmessage(), pq_startmsgread(), and PqMsg_PasswordMessage.
Referenced by CheckMD5Auth(), and CheckPasswordAuth().
◆ sendAuthRequest()
Definition at line 682 of file auth.c.
References AUTH_REQ_OK, AUTH_REQ_SASL_FIN, buf, CHECK_FOR_INTERRUPTS, fb(), pq_beginmessage(), pq_endmessage(), pq_flush, pq_sendbytes(), pq_sendint32(), and PqMsg_AuthenticationRequest.
Referenced by CheckMD5Auth(), CheckPasswordAuth(), CheckSASLAuth(), and ClientAuthentication().
◆ set_authn_id()
Definition at line 336 of file auth.c.
References Assert, ClientConnectionInfo::auth_method, ClientConnectionInfo::authn_id, ereport, errdetail_log(), errmsg, FATAL, hba_authname(), LOG, LOG_CONNECTION_AUTHENTICATION, log_connections, MemoryContextStrdup(), MyClientConnectionInfo, port, and TopMemoryContext.
Referenced by auth_peer(), CheckPasswordAuth(), CheckPWChallengeAuth(), ident_inet(), and validate().
Variable Documentation
◆ ClientAuthentication_hook
| ClientAuthentication_hook_type ClientAuthentication_hook = NULL |
Definition at line 217 of file auth.c.
Referenced by _PG_init(), ClientAuthentication(), and sepgsql_init_client_label().
◆ pg_gss_accept_delegation
| bool pg_gss_accept_delegation |
Definition at line 176 of file auth.c.
Referenced by secure_open_gssapi().
◆ pg_krb_caseins_users
◆ pg_krb_server_keyfile
| char* pg_krb_server_keyfile |
Definition at line 174 of file auth.c.
Referenced by secure_open_gssapi().