#include "postgres.h"#include <unistd.h>#include "access/xlog.h"#include "catalog/pg_control.h"#include "common/base64.h"#include "common/hmac.h"#include "common/saslprep.h"#include "common/scram-common.h"#include "common/sha2.h"#include "libpq/crypt.h"#include "libpq/sasl.h"#include "libpq/scram.h"#include "miscadmin.h"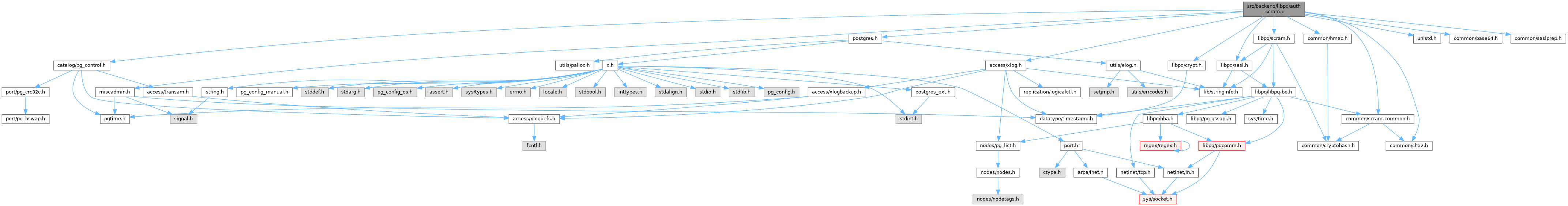
Go to the source code of this file.
Data Structures | |
| struct | scram_state |
Enumerations | |
| enum | scram_state_enum { SCRAM_AUTH_INIT , SCRAM_AUTH_SALT_SENT , SCRAM_AUTH_FINISHED } |
Variables | |
| const pg_be_sasl_mech | pg_be_scram_mech |
| int | scram_sha_256_iterations = SCRAM_SHA_256_DEFAULT_ITERATIONS |
Enumeration Type Documentation
◆ scram_state_enum
| Enumerator | |
|---|---|
| SCRAM_AUTH_INIT | |
| SCRAM_AUTH_SALT_SENT | |
| SCRAM_AUTH_FINISHED | |
Definition at line 126 of file auth-scram.c.
Function Documentation
◆ build_server_final_message()
|
static |
Definition at line 1410 of file auth-scram.c.
References elog, ERROR, fb(), palloc(), pg_b64_enc_len(), pg_b64_encode(), pg_hmac_create(), pg_hmac_error(), pg_hmac_final(), pg_hmac_free(), pg_hmac_init(), pg_hmac_update(), psprintf(), and SCRAM_MAX_KEY_LEN.
Referenced by scram_exchange().
◆ build_server_first_message()
|
static |
Definition at line 1200 of file auth-scram.c.
References ereport, errcode(), errmsg, ERROR, fb(), palloc(), pg_b64_enc_len(), pg_b64_encode(), pg_strong_random(), psprintf(), pstrdup(), and SCRAM_RAW_NONCE_LEN.
Referenced by scram_exchange().
◆ is_scram_printable()
Definition at line 777 of file auth-scram.c.
References fb().
Referenced by read_client_first_message().
◆ mock_scram_secret()
|
static |
Definition at line 695 of file auth-scram.c.
References elog, ERROR, fb(), iterations, palloc(), pg_b64_enc_len(), pg_b64_encode(), PG_SHA256, SCRAM_DEFAULT_SALT_LEN, SCRAM_MAX_KEY_LEN, scram_mock_salt(), SCRAM_SHA_256_DEFAULT_ITERATIONS, SCRAM_SHA_256_KEY_LEN, and username.
Referenced by scram_init().
◆ parse_scram_secret()
| bool parse_scram_secret | ( | const char * | secret, |
| int * | iterations, | ||
| pg_cryptohash_type * | hash_type, | ||
| int * | key_length, | ||
| char ** | salt, | ||
| uint8 * | stored_key, | ||
| uint8 * | server_key | ||
| ) |
Definition at line 598 of file auth-scram.c.
References fb(), iterations, memcpy(), palloc(), pg_b64_dec_len(), pg_b64_decode(), PG_SHA256, pstrdup(), SCRAM_SHA_256_KEY_LEN, and strsep().
Referenced by get_password_type(), scram_init(), and scram_verify_plain_password().
◆ pg_be_scram_build_secret()
Definition at line 481 of file auth-scram.c.
References ereport, errcode(), errmsg, ERROR, fb(), password, pfree(), pg_saslprep(), PG_SHA256, pg_strong_random(), result, SASLPREP_SUCCESS, scram_build_secret(), SCRAM_DEFAULT_SALT_LEN, scram_sha_256_iterations, and SCRAM_SHA_256_KEY_LEN.
Referenced by encrypt_password().
◆ read_any_attr()
Definition at line 853 of file auth-scram.c.
References ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errdetail(), errmsg, ERROR, fb(), input, and sanitize_char().
Referenced by read_client_final_message(), and read_client_first_message().
◆ read_attr_value()
Definition at line 741 of file auth-scram.c.
References ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errdetail(), errmsg, ERROR, input, and sanitize_char().
Referenced by read_client_final_message(), and read_client_first_message().
◆ read_client_final_message()
|
static |
Definition at line 1264 of file auth-scram.c.
References Assert, be_tls_get_certificate_hash(), elog, ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errdetail(), errmsg, ERROR, fb(), input, memcpy(), palloc(), pfree(), pg_b64_dec_len(), pg_b64_decode(), pg_b64_enc_len(), pg_b64_encode(), pstrdup(), read_any_attr(), read_attr_value(), snprintf, and value.
Referenced by scram_exchange().
◆ read_client_first_message()
|
static |
Definition at line 911 of file auth-scram.c.
References ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errdetail(), errmsg, ERROR, fb(), input, is_scram_printable(), pstrdup(), read_any_attr(), read_attr_value(), sanitize_char(), and sanitize_str().
Referenced by scram_exchange().
◆ sanitize_char()
Definition at line 805 of file auth-scram.c.
Referenced by read_any_attr(), read_attr_value(), and read_client_first_message().
◆ sanitize_str()
Definition at line 825 of file auth-scram.c.
Referenced by read_client_first_message().
◆ scram_exchange()
|
static |
Definition at line 350 of file auth-scram.c.
References Assert, build_server_final_message(), build_server_first_message(), elog, ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errdetail(), errmsg, ERROR, fb(), Port::has_scram_keys, input, memcpy(), MyProcPort, output, PG_SASL_EXCHANGE_CONTINUE, PG_SASL_EXCHANGE_FAILURE, PG_SASL_EXCHANGE_SUCCESS, pstrdup(), read_client_final_message(), read_client_first_message(), result, SCRAM_AUTH_FINISHED, SCRAM_AUTH_INIT, SCRAM_AUTH_SALT_SENT, Port::scram_ClientKey, Port::scram_ServerKey, verify_client_proof(), and verify_final_nonce().
◆ scram_get_mechanisms()
|
static |
Definition at line 204 of file auth-scram.c.
References appendStringInfoChar(), appendStringInfoString(), buf, port, SCRAM_SHA_256_NAME, and SCRAM_SHA_256_PLUS_NAME.
◆ scram_init()
|
static |
Definition at line 238 of file auth-scram.c.
References _, ereport, errcode(), ERRCODE_PROTOCOL_VIOLATION, errmsg, ERROR, fb(), get_password_type(), LOG, mock_scram_secret(), palloc0_object, parse_scram_secret(), PASSWORD_TYPE_SCRAM_SHA_256, port, psprintf(), SCRAM_AUTH_INIT, SCRAM_SHA_256_NAME, and SCRAM_SHA_256_PLUS_NAME.
◆ scram_mock_salt()
|
static |
Definition at line 1469 of file auth-scram.c.
References Assert, fb(), GetMockAuthenticationNonce(), MOCK_AUTH_NONCE_LEN, pg_cryptohash_create(), pg_cryptohash_final(), pg_cryptohash_free(), pg_cryptohash_init(), pg_cryptohash_update(), PG_SHA256, PG_SHA256_DIGEST_LENGTH, SCRAM_DEFAULT_SALT_LEN, SCRAM_MAX_KEY_LEN, StaticAssertDecl, and username.
Referenced by mock_scram_secret().
◆ scram_verify_plain_password()
| bool scram_verify_plain_password | ( | const char * | username, |
| const char * | password, | ||
| const char * | secret | ||
| ) |
Definition at line 521 of file auth-scram.c.
References elog, ereport, errmsg, ERROR, fb(), iterations, LOG, palloc(), parse_scram_secret(), password, pfree(), pg_b64_dec_len(), pg_b64_decode(), pg_saslprep(), SASLPREP_SUCCESS, SCRAM_MAX_KEY_LEN, scram_SaltedPassword(), scram_ServerKey(), timingsafe_bcmp(), and username.
Referenced by plain_crypt_verify().
◆ verify_client_proof()
|
static |
Definition at line 1147 of file auth-scram.c.
References elog, ERROR, fb(), i, pg_hmac_create(), pg_hmac_error(), pg_hmac_final(), pg_hmac_free(), pg_hmac_init(), pg_hmac_update(), scram_H(), SCRAM_MAX_KEY_LEN, and timingsafe_bcmp().
Referenced by scram_exchange().
◆ verify_final_nonce()
|
static |
Definition at line 1125 of file auth-scram.c.
References fb(), and timingsafe_bcmp().
Referenced by scram_exchange().
Variable Documentation
◆ pg_be_scram_mech
| const pg_be_sasl_mech pg_be_scram_mech |
Definition at line 114 of file auth-scram.c.
Referenced by CheckPWChallengeAuth().
◆ scram_sha_256_iterations
| int scram_sha_256_iterations = SCRAM_SHA_256_DEFAULT_ITERATIONS |
Definition at line 194 of file auth-scram.c.
Referenced by pg_be_scram_build_secret().