#include "postgres_fe.h"#include <arpa/inet.h>#include "fe-secure-common.h"#include "libpq-int.h"#include "pqexpbuffer.h"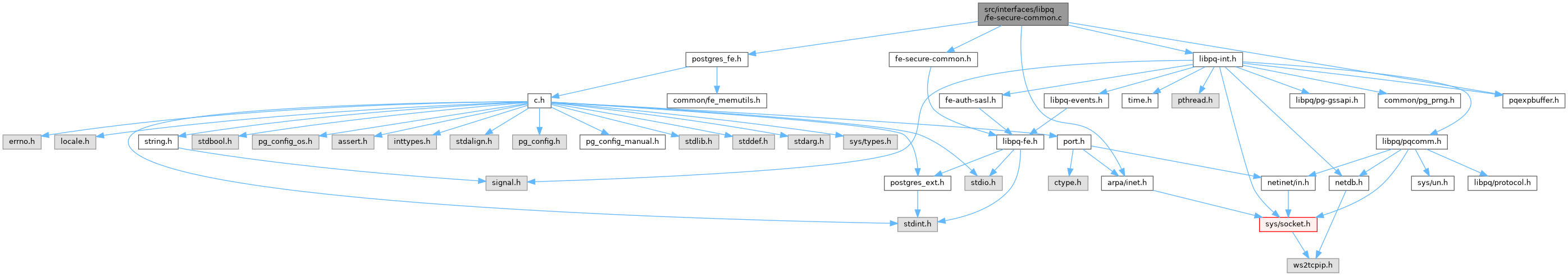
Go to the source code of this file.
Functions | |
| static bool | wildcard_certificate_match (const char *pattern, const char *string) |
| int | pq_verify_peer_name_matches_certificate_name (PGconn *conn, const char *namedata, size_t namelen, char **store_name) |
| int | pq_verify_peer_name_matches_certificate_ip (PGconn *conn, const unsigned char *ipdata, size_t iplen, char **store_name) |
| bool | pq_verify_peer_name_matches_certificate (PGconn *conn) |
Function Documentation
◆ pq_verify_peer_name_matches_certificate()
Definition at line 252 of file fe-secure-common.c.
References appendPQExpBuffer(), appendPQExpBufferChar(), conn, pg_conn::connhost, pg_conn::errorMessage, fb(), free, pg_conn_host::host, libpq_append_conn_error(), libpq_ngettext, pgtls_verify_peer_name_matches_certificate_guts(), pg_conn::sslmode, and pg_conn::whichhost.
Referenced by open_client_SSL().
◆ pq_verify_peer_name_matches_certificate_ip()
| int pq_verify_peer_name_matches_certificate_ip | ( | PGconn * | conn, |
| const unsigned char * | ipdata, | ||
| size_t | iplen, | ||
| char ** | store_name | ||
| ) |
Definition at line 157 of file fe-secure-common.c.
References conn, pg_conn::connhost, fb(), pg_conn_host::host, inet_aton(), libpq_append_conn_error(), pg_inet_net_ntop(), PG_STRERROR_R_BUFLEN, strerror_r, and pg_conn::whichhost.
Referenced by openssl_verify_peer_name_matches_certificate_ip().
◆ pq_verify_peer_name_matches_certificate_name()
| int pq_verify_peer_name_matches_certificate_name | ( | PGconn * | conn, |
| const char * | namedata, | ||
| size_t | namelen, | ||
| char ** | store_name | ||
| ) |
Definition at line 87 of file fe-secure-common.c.
References conn, pg_conn::connhost, fb(), free, pg_conn_host::host, libpq_append_conn_error(), malloc, memcpy(), name, pg_strcasecmp(), result, pg_conn::whichhost, and wildcard_certificate_match().
Referenced by openssl_verify_peer_name_matches_certificate_name().
◆ wildcard_certificate_match()
Definition at line 45 of file fe-secure-common.c.
References fb(), and pg_strcasecmp().
Referenced by pq_verify_peer_name_matches_certificate_name().