#include "postgres_fe.h"#include "fe-gssapi-common.h"#include "libpq-fe.h"#include "libpq-int.h"#include "port/pg_bswap.h"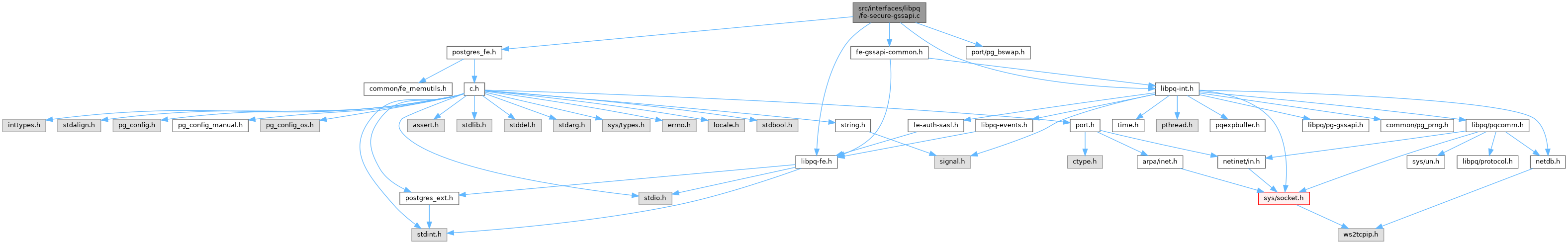
Go to the source code of this file.
Macros | |
| #define | GSS_REQUIRED_FLAGS |
| #define | PQ_GSS_MAX_PACKET_SIZE 16384 /* includes uint32 header word */ |
| #define | PQ_GSS_AUTH_BUFFER_SIZE 65536 /* includes uint32 header word */ |
| #define | PqGSSSendBuffer (conn->gss_SendBuffer) |
| #define | PqGSSSendLength (conn->gss_SendLength) |
| #define | PqGSSSendNext (conn->gss_SendNext) |
| #define | PqGSSSendConsumed (conn->gss_SendConsumed) |
| #define | PqGSSRecvBuffer (conn->gss_RecvBuffer) |
| #define | PqGSSRecvLength (conn->gss_RecvLength) |
| #define | PqGSSResultBuffer (conn->gss_ResultBuffer) |
| #define | PqGSSResultLength (conn->gss_ResultLength) |
| #define | PqGSSResultNext (conn->gss_ResultNext) |
| #define | PqGSSMaxPktSize (conn->gss_MaxPktSize) |
Functions | |
| ssize_t | pg_GSS_write (PGconn *conn, const void *ptr, size_t len) |
| ssize_t | pg_GSS_read (PGconn *conn, void *ptr, size_t len) |
| static PostgresPollingStatusType | gss_read (PGconn *conn, void *recv_buffer, size_t length, ssize_t *ret) |
| PostgresPollingStatusType | pqsecure_open_gss (PGconn *conn) |
| void * | PQgetgssctx (PGconn *conn) |
| int | PQgssEncInUse (PGconn *conn) |
Macro Definition Documentation
◆ GSS_REQUIRED_FLAGS
| #define GSS_REQUIRED_FLAGS |
Definition at line 26 of file fe-secure-gssapi.c.
◆ PQ_GSS_AUTH_BUFFER_SIZE
Definition at line 61 of file fe-secure-gssapi.c.
◆ PQ_GSS_MAX_PACKET_SIZE
Definition at line 53 of file fe-secure-gssapi.c.
◆ PqGSSMaxPktSize
| #define PqGSSMaxPktSize (conn->gss_MaxPktSize) |
Definition at line 77 of file fe-secure-gssapi.c.
◆ PqGSSRecvBuffer
| #define PqGSSRecvBuffer (conn->gss_RecvBuffer) |
Definition at line 72 of file fe-secure-gssapi.c.
◆ PqGSSRecvLength
| #define PqGSSRecvLength (conn->gss_RecvLength) |
Definition at line 73 of file fe-secure-gssapi.c.
◆ PqGSSResultBuffer
| #define PqGSSResultBuffer (conn->gss_ResultBuffer) |
Definition at line 74 of file fe-secure-gssapi.c.
◆ PqGSSResultLength
| #define PqGSSResultLength (conn->gss_ResultLength) |
Definition at line 75 of file fe-secure-gssapi.c.
◆ PqGSSResultNext
| #define PqGSSResultNext (conn->gss_ResultNext) |
Definition at line 76 of file fe-secure-gssapi.c.
◆ PqGSSSendBuffer
| #define PqGSSSendBuffer (conn->gss_SendBuffer) |
Definition at line 68 of file fe-secure-gssapi.c.
◆ PqGSSSendConsumed
| #define PqGSSSendConsumed (conn->gss_SendConsumed) |
Definition at line 71 of file fe-secure-gssapi.c.
◆ PqGSSSendLength
| #define PqGSSSendLength (conn->gss_SendLength) |
Definition at line 69 of file fe-secure-gssapi.c.
◆ PqGSSSendNext
| #define PqGSSSendNext (conn->gss_SendNext) |
Definition at line 70 of file fe-secure-gssapi.c.
Function Documentation
◆ gss_read()
|
static |
Definition at line 435 of file fe-secure-gssapi.c.
References conn, EAGAIN, EINTR, EWOULDBLOCK, fb(), PGRES_POLLING_FAILED, PGRES_POLLING_OK, PGRES_POLLING_READING, pqReadReady(), pqsecure_raw_read(), result, and SOCK_ERRNO.
Referenced by pqsecure_open_gss().
◆ pg_GSS_read()
Definition at line 266 of file fe-secure-gssapi.c.
References Assert, cleanup(), conn, EWOULDBLOCK, fb(), input, len, libpq_append_conn_error(), libpq_gettext, memcpy(), Min, output, pg_GSS_error(), pg_ntoh32, PQ_GSS_MAX_PACKET_SIZE, PqGSSRecvBuffer, PqGSSRecvLength, PqGSSResultBuffer, PqGSSResultLength, PqGSSResultNext, pqsecure_raw_read(), and SOCK_ERRNO_SET.
Referenced by pqsecure_read().
◆ pg_GSS_write()
Definition at line 93 of file fe-secure-gssapi.c.
References appendPQExpBufferStr(), Assert, cleanup(), conn, pg_conn::errorMessage, fb(), input, len, libpq_append_conn_error(), libpq_gettext, memcpy(), output, pg_GSS_error(), pg_hton32, PQ_GSS_MAX_PACKET_SIZE, PqGSSMaxPktSize, PqGSSSendBuffer, PqGSSSendConsumed, PqGSSSendLength, PqGSSSendNext, pqsecure_raw_write(), and SOCK_ERRNO_SET.
Referenced by pqsecure_write().
◆ PQgetgssctx()
◆ PQgssEncInUse()
◆ pqsecure_open_gss()
| PostgresPollingStatusType pqsecure_open_gss | ( | PGconn * | conn | ) |
Definition at line 481 of file fe-secure-gssapi.c.
References appendPQExpBuffer(), Assert, conn, EAGAIN, EINTR, pg_conn::errorMessage, EWOULDBLOCK, fb(), free, gss_read(), GSS_REQUIRED_FLAGS, pg_conn::gssapi_used, pg_conn::gssdelegation, input, libpq_append_conn_error(), libpq_gettext, malloc, memcpy(), output, pg_GSS_error(), pg_GSS_have_cred_cache(), pg_GSS_load_servicename(), pg_hton32, pg_ntoh32, PGRES_POLLING_FAILED, PGRES_POLLING_OK, PGRES_POLLING_READING, PGRES_POLLING_WRITING, PQ_GSS_AUTH_BUFFER_SIZE, PQ_GSS_MAX_PACKET_SIZE, PqGSSMaxPktSize, PqGSSRecvBuffer, PqGSSRecvLength, PqGSSResultBuffer, PqGSSResultLength, PqGSSResultNext, PqGSSSendBuffer, PqGSSSendConsumed, PqGSSSendLength, PqGSSSendNext, pqsecure_raw_write(), result, SOCK_ERRNO, and STATUS_OK.
Referenced by PQconnectPoll().