Definition at line 33 of file usercontext.c.
34{
35
38
39
43 errmsg(
"role \"%s\" cannot SET ROLE to \"%s\"",
46
47
48
49
50
51
53 {
54
55
56
57
58
61 }
62 else
63 {
65
66
67
68
69
70
71
72
73
77 }
78}
bool member_can_set_role(Oid member, Oid role)
int errcode(int sqlerrcode)
#define ereport(elevel,...)
int NewGUCNestLevel(void)
#define SECURITY_RESTRICTED_OPERATION
void GetUserIdAndSecContext(Oid *userid, int *sec_context)
char * GetUserNameFromId(Oid roleid, bool noerr)
References ereport, errcode(), errmsg, ERROR, fb(), GetUserIdAndSecContext(), GetUserNameFromId(), member_can_set_role(), NewGUCNestLevel(), UserContext::save_nestlevel, UserContext::save_sec_context, UserContext::save_userid, SECURITY_RESTRICTED_OPERATION, and SetUserIdAndSecContext().
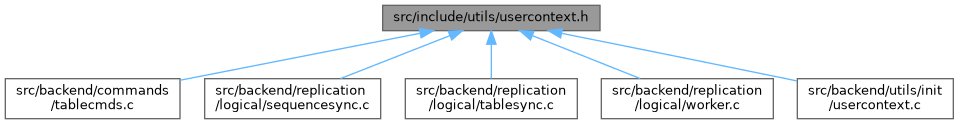
Referenced by apply_handle_delete(), apply_handle_insert(), apply_handle_update(), copy_sequence(), ExecuteTruncateGuts(), and LogicalRepSyncTableStart().