#include "common/cryptohash.h"#include "lib/stringinfo.h"#include "libpq/libpq-be.h"#include "libpq/sasl.h"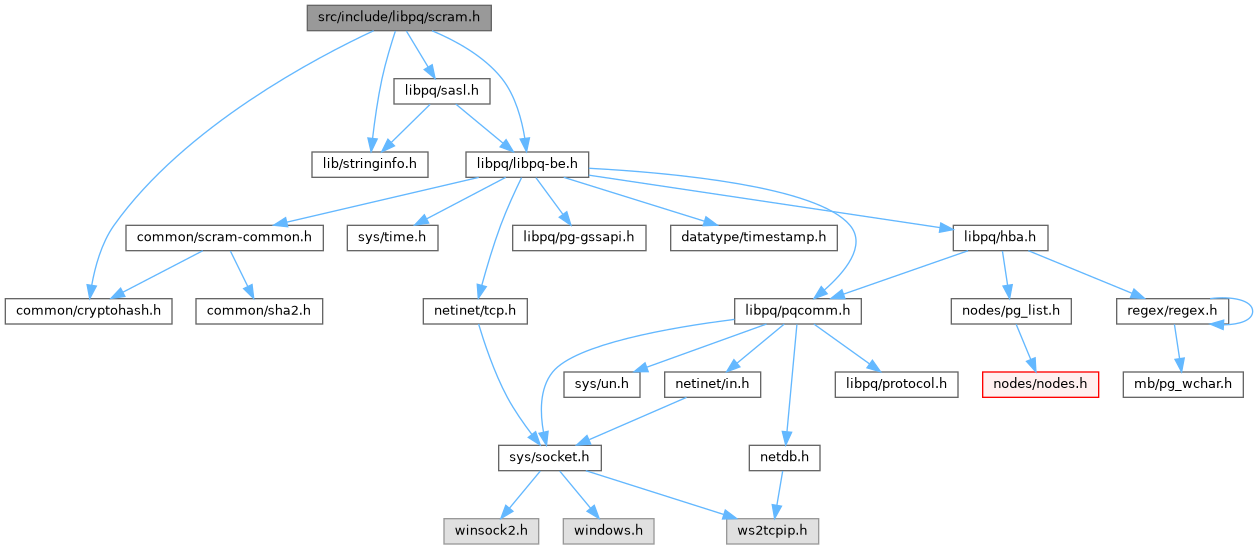
Go to the source code of this file.
Functions | |
| char * | pg_be_scram_build_secret (const char *password) |
| bool | parse_scram_secret (const char *secret, int *iterations, pg_cryptohash_type *hash_type, int *key_length, char **salt, uint8 *stored_key, uint8 *server_key) |
| bool | scram_verify_plain_password (const char *username, const char *password, const char *secret) |
Variables | |
| PGDLLIMPORT int | scram_sha_256_iterations |
| PGDLLIMPORT const pg_be_sasl_mech | pg_be_scram_mech |
Function Documentation
◆ parse_scram_secret()
|
extern |
Definition at line 598 of file auth-scram.c.
References fb(), iterations, memcpy(), palloc(), pg_b64_dec_len(), pg_b64_decode(), PG_SHA256, pstrdup(), SCRAM_SHA_256_KEY_LEN, and strsep().
Referenced by get_password_type(), scram_init(), and scram_verify_plain_password().
◆ pg_be_scram_build_secret()
Definition at line 481 of file auth-scram.c.
References ereport, errcode(), errmsg, ERROR, fb(), password, pfree(), pg_saslprep(), PG_SHA256, pg_strong_random(), result, SASLPREP_SUCCESS, scram_build_secret(), SCRAM_DEFAULT_SALT_LEN, scram_sha_256_iterations, and SCRAM_SHA_256_KEY_LEN.
Referenced by encrypt_password().
◆ scram_verify_plain_password()
|
extern |
Definition at line 521 of file auth-scram.c.
References elog, ereport, errmsg, ERROR, fb(), iterations, LOG, palloc(), parse_scram_secret(), password, pfree(), pg_b64_dec_len(), pg_b64_decode(), pg_saslprep(), SASLPREP_SUCCESS, SCRAM_MAX_KEY_LEN, scram_SaltedPassword(), scram_ServerKey(), timingsafe_bcmp(), and username.
Referenced by plain_crypt_verify().
Variable Documentation
◆ pg_be_scram_mech
|
extern |
Definition at line 114 of file auth-scram.c.
Referenced by CheckPWChallengeAuth().
◆ scram_sha_256_iterations
|
extern |
Definition at line 194 of file auth-scram.c.
Referenced by pg_be_scram_build_secret().