#include "postgres_fe.h"#include <unistd.h>#include <fcntl.h>#include <limits.h>#include <pwd.h>#include <sys/param.h>#include <sys/socket.h>#include <netdb.h>#include "common/md5.h"#include "common/oauth-common.h"#include "common/scram-common.h"#include "fe-auth.h"#include "fe-auth-sasl.h"#include "fe-auth-oauth.h"#include "libpq-fe.h"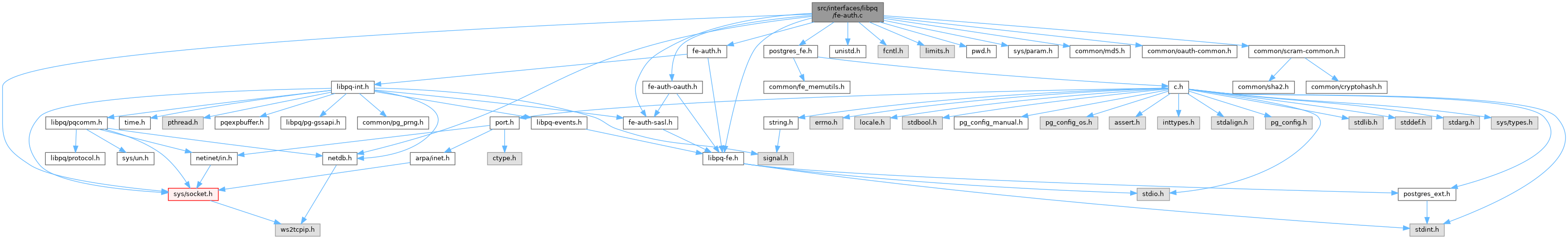
Go to the source code of this file.
Macros | |
| #define | auth_method_allowed(conn, type) (((conn)->allowed_auth_methods & (1 << (type))) != 0) |
| #define | MAX_ALGORITHM_NAME_LEN 50 |
Functions | |
| static int | pg_SASL_init (PGconn *conn, int payloadlen, bool *async) |
| static int | pg_SASL_continue (PGconn *conn, int payloadlen, bool final, bool *async) |
| static int | pg_password_sendauth (PGconn *conn, const char *password, AuthRequest areq) |
| static const char * | auth_method_description (AuthRequest areq) |
| static bool | check_expected_areq (AuthRequest areq, PGconn *conn) |
| int | pg_fe_sendauth (AuthRequest areq, int payloadlen, PGconn *conn, bool *async) |
| char * | pg_fe_getusername (uid_t user_id, PQExpBuffer errorMessage) |
| char * | pg_fe_getauthname (PQExpBuffer errorMessage) |
| char * | PQencryptPassword (const char *passwd, const char *user) |
| char * | PQencryptPasswordConn (PGconn *conn, const char *passwd, const char *user, const char *algorithm) |
| PGresult * | PQchangePassword (PGconn *conn, const char *user, const char *passwd) |
| PQauthDataHook_type | PQgetAuthDataHook (void) |
| void | PQsetAuthDataHook (PQauthDataHook_type hook) |
| int | PQdefaultAuthDataHook (PGauthData type, PGconn *conn, void *data) |
Variables | |
| PQauthDataHook_type | PQauthDataHook = PQdefaultAuthDataHook |
Macro Definition Documentation
◆ auth_method_allowed
Definition at line 894 of file fe-auth.c.
◆ MAX_ALGORITHM_NAME_LEN
| #define MAX_ALGORITHM_NAME_LEN 50 |
Function Documentation
◆ auth_method_description()
|
static |
Definition at line 868 of file fe-auth.c.
References AUTH_REQ_GSS, AUTH_REQ_GSS_CONT, AUTH_REQ_MD5, AUTH_REQ_PASSWORD, AUTH_REQ_SASL, AUTH_REQ_SASL_CONT, AUTH_REQ_SASL_FIN, AUTH_REQ_SSPI, fb(), and libpq_gettext.
Referenced by check_expected_areq().
◆ check_expected_areq()
|
static |
Definition at line 903 of file fe-auth.c.
References pg_conn::allowed_auth_methods, auth_method_allowed, auth_method_description(), AUTH_REQ_GSS, AUTH_REQ_GSS_CONT, AUTH_REQ_MAX, AUTH_REQ_MD5, AUTH_REQ_OK, AUTH_REQ_PASSWORD, AUTH_REQ_SASL, AUTH_REQ_SASL_CONT, AUTH_REQ_SASL_FIN, AUTH_REQ_SSPI, pg_conn::auth_required, pg_conn::channel_binding, pg_fe_sasl_mech::channel_bound, pg_conn::client_finished_auth, conn, fb(), libpq_append_conn_error(), libpq_gettext, pg_conn::require_auth, result, pg_conn::sasl, pg_conn::sasl_state, pg_conn::ssl_cert_requested, pg_conn::ssl_cert_sent, pg_conn::sslcertmode, and StaticAssertDecl.
Referenced by pg_fe_sendauth().
◆ pg_fe_getauthname()
| char * pg_fe_getauthname | ( | PQExpBuffer | errorMessage | ) |
Definition at line 1344 of file fe-auth.c.
References fb(), and pg_fe_getusername().
Referenced by conninfo_add_defaults(), and pqConnectOptions2().
◆ pg_fe_getusername()
| char * pg_fe_getusername | ( | uid_t | user_id, |
| PQExpBuffer | errorMessage | ||
| ) |
Definition at line 1286 of file fe-auth.c.
References buf, fb(), libpq_append_error(), name, result, and username.
Referenced by pg_fe_getauthname(), and PQconnectPoll().
◆ pg_fe_sendauth()
| int pg_fe_sendauth | ( | AuthRequest | areq, |
| int | payloadlen, | ||
| PGconn * | conn, | ||
| bool * | async | ||
| ) |
Definition at line 1066 of file fe-auth.c.
References appendPQExpBufferStr(), AUTH_REQ_CRYPT, AUTH_REQ_GSS, AUTH_REQ_GSS_CONT, AUTH_REQ_KRB4, AUTH_REQ_KRB5, AUTH_REQ_MD5, AUTH_REQ_OK, AUTH_REQ_PASSWORD, AUTH_REQ_SASL, AUTH_REQ_SASL_CONT, AUTH_REQ_SASL_FIN, AUTH_REQ_SSPI, check_expected_areq(), pg_conn::client_finished_auth, conn, pg_conn::connhost, pg_conn::errorMessage, fb(), pg_conn::gsslib, PQExpBufferData::len, libpq_append_conn_error(), password, pg_conn_host::password, pg_conn::password_needed, pg_password_sendauth(), pg_SASL_continue(), pg_SASL_init(), pg_strcasecmp(), pglock_thread, pg_conn::pgpass, pgunlock_thread, PQnoPasswordSupplied, pg_conn::sasl_state, STATUS_ERROR, STATUS_OK, and pg_conn::whichhost.
Referenced by PQconnectPoll().
◆ pg_password_sendauth()
Definition at line 796 of file fe-auth.c.
References AUTH_REQ_MD5, AUTH_REQ_PASSWORD, AUTH_RESPONSE_PASSWORD, conn, pg_conn::current_auth_response, fb(), free, pg_conn::inBuffer, pg_conn::inStart, libpq_append_conn_error(), malloc, MD5_PASSWD_LEN, password, pg_conn::Pfdebug, pg_md5_encrypt(), pg_conn::pguser, pqGetnchar(), PqMsg_PasswordMessage, pqPacketSend(), pqTraceOutputMessage(), and STATUS_ERROR.
Referenced by pg_fe_sendauth().
◆ pg_SASL_continue()
Definition at line 704 of file fe-auth.c.
References AUTH_RESPONSE_SASL, conn, pg_conn::current_auth_response, pg_fe_sasl_mech::exchange, fb(), free, pg_conn::inBuffer, pg_conn::inStart, libpq_append_conn_error(), malloc, output, pg_conn::Pfdebug, pqGetnchar(), PqMsg_SASLResponse, pqPacketSend(), pqTraceOutputMessage(), pg_conn::sasl, SASL_ASYNC, SASL_CONTINUE, SASL_FAILED, pg_conn::sasl_state, STATUS_ERROR, and STATUS_OK.
Referenced by pg_fe_sendauth().
◆ pg_SASL_init()
Definition at line 435 of file fe-auth.c.
References pg_conn::allowed_sasl_mechs, appendPQExpBufferStr(), Assert, pg_conn::async_auth, AUTH_RESPONSE_SASL_INITIAL, pg_conn::channel_binding, pg_conn::cleanup_async_auth, conn, pg_conn::connhost, pg_conn::current_auth_response, error(), pg_conn::errorMessage, pg_fe_sasl_mech::exchange, fb(), free, i, pg_conn::inBuffer, pg_fe_sasl_mech::init, initPQExpBuffer(), pg_conn::inStart, lengthof, libpq_append_conn_error(), OAUTHBEARER_NAME, password, pg_conn_host::password, pg_conn::password_needed, pg_conn::Pfdebug, pg_oauth_mech, pg_scram_mech, pg_conn::pgpass, PQExpBufferDataBroken, pqFlush(), pqGets(), PqMsg_SASLInitialResponse, PQnoPasswordSupplied, pqPutInt(), pqPutMsgEnd(), pqPutMsgStart(), pqPutnchar(), pqPuts(), pqTraceOutputMessage(), pg_conn::require_auth, pg_conn::sasl, SASL_ASYNC, SASL_FAILED, pg_conn::sasl_state, pg_conn::scram_client_key_binary, SCRAM_SHA_256_NAME, SCRAM_SHA_256_PLUS_NAME, pg_conn::ssl_in_use, STATUS_ERROR, STATUS_OK, termPQExpBuffer(), and pg_conn::whichhost.
Referenced by pg_fe_sendauth().
◆ PQchangePassword()
Definition at line 1531 of file fe-auth.c.
References buf, conn, fb(), initPQExpBuffer(), PQencryptPasswordConn(), PQescapeIdentifier(), PQescapeLiteral(), PQexec(), PQfreemem(), printfPQExpBuffer(), termPQExpBuffer(), and user.
Referenced by exec_command_password().
◆ PQdefaultAuthDataHook()
| int PQdefaultAuthDataHook | ( | PGauthData | type, |
| PGconn * | conn, | ||
| void * | data | ||
| ) |
Definition at line 1601 of file fe-auth.c.
Referenced by PQsetAuthDataHook().
◆ PQencryptPassword()
Definition at line 1363 of file fe-auth.c.
References fb(), free, malloc, MD5_PASSWD_LEN, pg_md5_encrypt(), and user.
◆ PQencryptPasswordConn()
| char * PQencryptPasswordConn | ( | PGconn * | conn, |
| const char * | passwd, | ||
| const char * | user, | ||
| const char * | algorithm | ||
| ) |
Definition at line 1406 of file fe-auth.c.
References conn, fb(), free, libpq_append_conn_error(), malloc, MAX_ALGORITHM_NAME_LEN, MD5_PASSWD_LEN, pg_fe_scram_build_secret(), pg_md5_encrypt(), PGRES_TUPLES_OK, PQclear, pqClearConnErrorState, PQexec(), PQgetvalue, PQnfields, PQntuples, PQresultStatus, pg_conn::scram_sha_256_iterations, user, and val.
Referenced by main(), and PQchangePassword().
◆ PQgetAuthDataHook()
| PQauthDataHook_type PQgetAuthDataHook | ( | void | ) |
◆ PQsetAuthDataHook()
| void PQsetAuthDataHook | ( | PQauthDataHook_type | hook | ) |
Definition at line 1595 of file fe-auth.c.
References PQauthDataHook, and PQdefaultAuthDataHook().
Referenced by main().
Variable Documentation
◆ PQauthDataHook
| PQauthDataHook_type PQauthDataHook = PQdefaultAuthDataHook |
Definition at line 1586 of file fe-auth.c.
Referenced by PQgetAuthDataHook(), PQsetAuthDataHook(), and setup_token_request().