#include "postgres.h"#include "catalog/pg_proc.h"#include "commands/seclabel.h"#include "common/hashfn.h"#include "sepgsql.h"#include "storage/ipc.h"#include "utils/guc.h"#include "utils/memutils.h"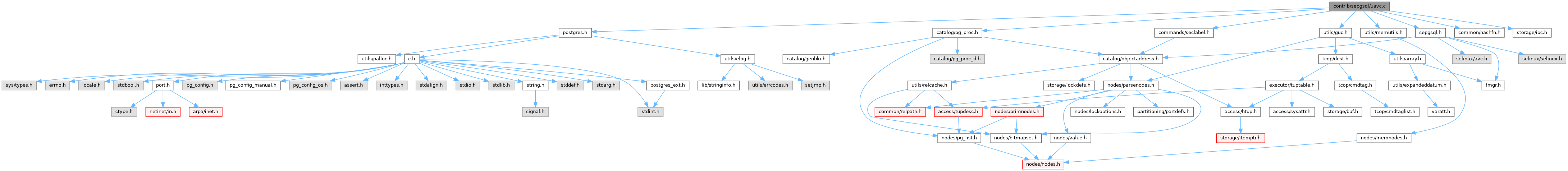
Go to the source code of this file.
Data Structures | |
| struct | avc_cache |
Macros | |
| #define | AVC_NUM_SLOTS 512 |
| #define | AVC_NUM_RECLAIM 16 |
| #define | AVC_DEF_THRESHOLD 384 |
Functions | |
| static uint32 | sepgsql_avc_hash (const char *scontext, const char *tcontext, uint16 tclass) |
| static void | sepgsql_avc_reset (void) |
| static void | sepgsql_avc_reclaim (void) |
| static bool | sepgsql_avc_check_valid (void) |
| static char * | sepgsql_avc_unlabeled (void) |
| static avc_cache * | sepgsql_avc_compute (const char *scontext, const char *tcontext, uint16 tclass) |
| static avc_cache * | sepgsql_avc_lookup (const char *scontext, const char *tcontext, uint16 tclass) |
| bool | sepgsql_avc_check_perms_label (const char *tcontext, uint16 tclass, uint32 required, const char *audit_name, bool abort_on_violation) |
| bool | sepgsql_avc_check_perms (const ObjectAddress *tobject, uint16 tclass, uint32 required, const char *audit_name, bool abort_on_violation) |
| char * | sepgsql_avc_trusted_proc (Oid functionId) |
| static void | sepgsql_avc_exit (int code, Datum arg) |
| void | sepgsql_avc_init (void) |
Variables | |
| static MemoryContext | avc_mem_cxt |
| static List * | avc_slots [AVC_NUM_SLOTS] |
| static int | avc_num_caches |
| static int | avc_lru_hint |
| static int | avc_threshold |
| static char * | avc_unlabeled |
Macro Definition Documentation
◆ AVC_DEF_THRESHOLD
◆ AVC_NUM_RECLAIM
◆ AVC_NUM_SLOTS
Function Documentation
◆ sepgsql_avc_check_perms()
| bool sepgsql_avc_check_perms | ( | const ObjectAddress * | tobject, |
| uint16 | tclass, | ||
| uint32 | required, | ||
| const char * | audit_name, | ||
| bool | abort_on_violation | ||
| ) |
Definition at line 420 of file uavc.c.
References fb(), GetSecurityLabel(), pfree(), sepgsql_avc_check_perms_label(), and SEPGSQL_LABEL_TAG.
Referenced by check_relation_privileges(), check_schema_perms(), sepgsql_attribute_drop(), sepgsql_attribute_relabel(), sepgsql_attribute_setattr(), sepgsql_database_drop(), sepgsql_database_relabel(), sepgsql_database_setattr(), sepgsql_fmgr_hook(), sepgsql_needs_fmgr_hook(), sepgsql_proc_drop(), sepgsql_proc_execute(), sepgsql_proc_post_create(), sepgsql_proc_relabel(), sepgsql_proc_setattr(), sepgsql_relation_drop(), sepgsql_relation_post_create(), sepgsql_relation_relabel(), sepgsql_relation_setattr(), sepgsql_relation_truncate(), sepgsql_schema_drop(), and sepgsql_schema_relabel().
◆ sepgsql_avc_check_perms_label()
| bool sepgsql_avc_check_perms_label | ( | const char * | tcontext, |
| uint16 | tclass, | ||
| uint32 | required, | ||
| const char * | audit_name, | ||
| bool | abort_on_violation | ||
| ) |
Definition at line 337 of file uavc.c.
References avc_cache::allowed, avc_cache::auditallow, avc_cache::auditdeny, ereport, errcode(), errmsg, ERROR, fb(), avc_cache::permissive, result, avc_cache::scontext, sepgsql_audit_log(), sepgsql_avc_check_valid(), sepgsql_avc_lookup(), SEPGSQL_AVC_NOAUDIT, sepgsql_avc_unlabeled(), sepgsql_get_client_label(), sepgsql_get_debug_audit(), sepgsql_get_mode(), sepgsql_getenforce(), SEPGSQL_MODE_INTERNAL, avc_cache::tclass, avc_cache::tcontext, and avc_cache::tcontext_is_valid.
Referenced by sepgsql_attribute_post_create(), sepgsql_attribute_relabel(), sepgsql_avc_check_perms(), sepgsql_database_post_create(), sepgsql_database_relabel(), sepgsql_fmgr_hook(), sepgsql_proc_post_create(), sepgsql_proc_relabel(), sepgsql_relation_post_create(), sepgsql_relation_relabel(), sepgsql_schema_post_create(), sepgsql_schema_relabel(), and sepgsql_set_client_label().
◆ sepgsql_avc_check_valid()
Definition at line 152 of file uavc.c.
References fb(), and sepgsql_avc_reset().
Referenced by sepgsql_avc_check_perms_label(), and sepgsql_avc_trusted_proc().
◆ sepgsql_avc_compute()
|
static |
Definition at line 200 of file uavc.c.
References avc_cache::allowed, avc_cache::auditallow, avc_cache::auditdeny, avc_mem_cxt, avc_num_caches, AVC_NUM_SLOTS, avc_slots, avc_threshold, fb(), avc_cache::hash, hash(), avc_cache::hot_cache, lcons(), MemoryContextSwitchTo(), avc_cache::ncontext, palloc0_object, avc_cache::permissive, pfree(), pstrdup(), avc_cache::scontext, SEPG_CLASS_DB_PROCEDURE, SEPG_CLASS_PROCESS, sepgsql_avc_hash(), sepgsql_avc_reclaim(), sepgsql_avc_unlabeled(), sepgsql_compute_avd(), sepgsql_compute_create(), avc_cache::tclass, avc_cache::tcontext, and avc_cache::tcontext_is_valid.
Referenced by sepgsql_avc_lookup().
◆ sepgsql_avc_exit()
◆ sepgsql_avc_hash()
|
static |
Definition at line 67 of file uavc.c.
References fb(), and hash_bytes().
Referenced by sepgsql_avc_compute(), and sepgsql_avc_lookup().
◆ sepgsql_avc_init()
Definition at line 488 of file uavc.c.
References ALLOCSET_DEFAULT_SIZES, AllocSetContextCreate, AVC_DEF_THRESHOLD, avc_lru_hint, avc_mem_cxt, avc_num_caches, avc_slots, avc_threshold, ereport, errcode(), errmsg, ERROR, fb(), LOG, on_proc_exit(), sepgsql_avc_exit(), and TopMemoryContext.
Referenced by _PG_init().
◆ sepgsql_avc_lookup()
|
static |
Definition at line 297 of file uavc.c.
References AVC_NUM_SLOTS, avc_slots, fb(), avc_cache::hash, hash(), avc_cache::hot_cache, lfirst, avc_cache::scontext, sepgsql_avc_compute(), sepgsql_avc_hash(), avc_cache::tclass, and avc_cache::tcontext.
Referenced by sepgsql_avc_check_perms_label(), and sepgsql_avc_trusted_proc().
◆ sepgsql_avc_reclaim()
Definition at line 92 of file uavc.c.
References avc_lru_hint, avc_num_caches, AVC_NUM_RECLAIM, AVC_NUM_SLOTS, avc_slots, avc_threshold, foreach_delete_current, avc_cache::hot_cache, lfirst, avc_cache::ncontext, pfree(), avc_cache::scontext, and avc_cache::tcontext.
Referenced by sepgsql_avc_compute().
◆ sepgsql_avc_reset()
Definition at line 78 of file uavc.c.
References avc_lru_hint, avc_mem_cxt, avc_num_caches, AVC_NUM_SLOTS, avc_slots, avc_unlabeled, fb(), and MemoryContextReset().
Referenced by sepgsql_avc_check_valid().
◆ sepgsql_avc_trusted_proc()
Definition at line 445 of file uavc.c.
References fb(), GetSecurityLabel(), avc_cache::ncontext, SEPG_CLASS_DB_PROCEDURE, sepgsql_avc_check_valid(), sepgsql_avc_lookup(), sepgsql_avc_unlabeled(), sepgsql_get_client_label(), and SEPGSQL_LABEL_TAG.
Referenced by sepgsql_fmgr_hook(), and sepgsql_needs_fmgr_hook().
◆ sepgsql_avc_unlabeled()
Definition at line 170 of file uavc.c.
References avc_mem_cxt, avc_unlabeled, ereport, errcode(), errmsg, ERROR, fb(), MemoryContextStrdup(), PG_END_TRY, PG_FINALLY, and PG_TRY.
Referenced by sepgsql_avc_check_perms_label(), sepgsql_avc_compute(), and sepgsql_avc_trusted_proc().
Variable Documentation
◆ avc_lru_hint
|
static |
Definition at line 59 of file uavc.c.
Referenced by sepgsql_avc_init(), sepgsql_avc_reclaim(), and sepgsql_avc_reset().
◆ avc_mem_cxt
|
static |
Definition at line 56 of file uavc.c.
Referenced by sepgsql_avc_compute(), sepgsql_avc_init(), sepgsql_avc_reset(), and sepgsql_avc_unlabeled().
◆ avc_num_caches
|
static |
Definition at line 58 of file uavc.c.
Referenced by sepgsql_avc_compute(), sepgsql_avc_init(), sepgsql_avc_reclaim(), and sepgsql_avc_reset().
◆ avc_slots
|
static |
Definition at line 57 of file uavc.c.
Referenced by sepgsql_avc_compute(), sepgsql_avc_init(), sepgsql_avc_lookup(), sepgsql_avc_reclaim(), and sepgsql_avc_reset().
◆ avc_threshold
|
static |
Definition at line 60 of file uavc.c.
Referenced by sepgsql_avc_compute(), sepgsql_avc_init(), and sepgsql_avc_reclaim().
◆ avc_unlabeled
|
static |
Definition at line 61 of file uavc.c.
Referenced by sepgsql_avc_reset(), and sepgsql_avc_unlabeled().