#include "catalog/objectaddress.h"#include "fmgr.h"#include <selinux/selinux.h>#include <selinux/avc.h>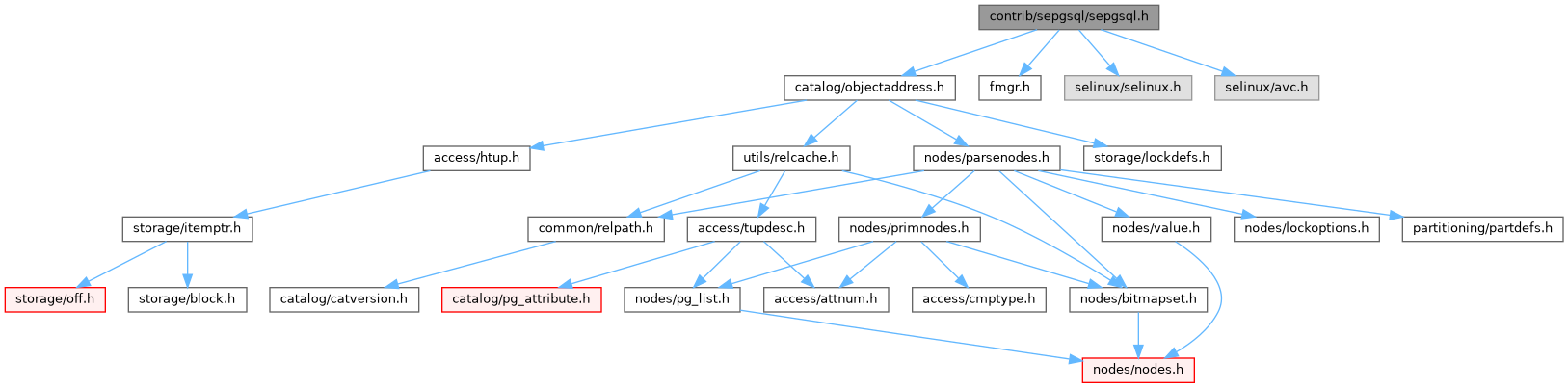
Go to the source code of this file.
Macro Definition Documentation
◆ SEPG_BLK_FILE__CREATE
| #define SEPG_BLK_FILE__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_BLK_FILE__GETATTR
| #define SEPG_BLK_FILE__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_BLK_FILE__READ
| #define SEPG_BLK_FILE__READ (SEPG_FILE__READ) |
◆ SEPG_BLK_FILE__RENAME
| #define SEPG_BLK_FILE__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_BLK_FILE__UNLINK
| #define SEPG_BLK_FILE__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_BLK_FILE__WRITE
| #define SEPG_BLK_FILE__WRITE (SEPG_FILE__WRITE) |
◆ SEPG_CHR_FILE__CREATE
| #define SEPG_CHR_FILE__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_CHR_FILE__GETATTR
| #define SEPG_CHR_FILE__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_CHR_FILE__READ
| #define SEPG_CHR_FILE__READ (SEPG_FILE__READ) |
◆ SEPG_CHR_FILE__RENAME
| #define SEPG_CHR_FILE__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_CHR_FILE__UNLINK
| #define SEPG_CHR_FILE__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_CHR_FILE__WRITE
| #define SEPG_CHR_FILE__WRITE (SEPG_FILE__WRITE) |
◆ SEPG_CLASS_BLK_FILE
◆ SEPG_CLASS_CHR_FILE
◆ SEPG_CLASS_DB_BLOB
◆ SEPG_CLASS_DB_COLUMN
◆ SEPG_CLASS_DB_DATABASE
◆ SEPG_CLASS_DB_LANGUAGE
◆ SEPG_CLASS_DB_PROCEDURE
◆ SEPG_CLASS_DB_SCHEMA
◆ SEPG_CLASS_DB_SEQUENCE
◆ SEPG_CLASS_DB_TABLE
◆ SEPG_CLASS_DB_TUPLE
◆ SEPG_CLASS_DB_VIEW
◆ SEPG_CLASS_DIR
◆ SEPG_CLASS_FIFO_FILE
◆ SEPG_CLASS_FILE
◆ SEPG_CLASS_LNK_FILE
◆ SEPG_CLASS_MAX
◆ SEPG_CLASS_PROCESS
◆ SEPG_CLASS_SOCK_FILE
◆ SEPG_DB_BLOB__CREATE
| #define SEPG_DB_BLOB__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_BLOB__DROP
| #define SEPG_DB_BLOB__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_BLOB__EXPORT
◆ SEPG_DB_BLOB__GETATTR
| #define SEPG_DB_BLOB__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_BLOB__IMPORT
◆ SEPG_DB_BLOB__READ
◆ SEPG_DB_BLOB__RELABELFROM
| #define SEPG_DB_BLOB__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_BLOB__RELABELTO
| #define SEPG_DB_BLOB__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_BLOB__SETATTR
| #define SEPG_DB_BLOB__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_BLOB__WRITE
◆ SEPG_DB_COLUMN__CREATE
| #define SEPG_DB_COLUMN__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_COLUMN__DROP
| #define SEPG_DB_COLUMN__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_COLUMN__GETATTR
| #define SEPG_DB_COLUMN__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_COLUMN__INSERT
◆ SEPG_DB_COLUMN__RELABELFROM
| #define SEPG_DB_COLUMN__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_COLUMN__RELABELTO
| #define SEPG_DB_COLUMN__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_COLUMN__SELECT
◆ SEPG_DB_COLUMN__SETATTR
| #define SEPG_DB_COLUMN__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_COLUMN__UPDATE
◆ SEPG_DB_DATABASE__ACCESS
◆ SEPG_DB_DATABASE__CREATE
◆ SEPG_DB_DATABASE__DROP
◆ SEPG_DB_DATABASE__GETATTR
◆ SEPG_DB_DATABASE__LOAD_MODULE
◆ SEPG_DB_DATABASE__RELABELFROM
◆ SEPG_DB_DATABASE__RELABELTO
◆ SEPG_DB_DATABASE__SETATTR
◆ SEPG_DB_LANGUAGE__CREATE
| #define SEPG_DB_LANGUAGE__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_LANGUAGE__DROP
| #define SEPG_DB_LANGUAGE__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_LANGUAGE__EXECUTE
◆ SEPG_DB_LANGUAGE__GETATTR
| #define SEPG_DB_LANGUAGE__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_LANGUAGE__IMPLEMENT
◆ SEPG_DB_LANGUAGE__RELABELFROM
| #define SEPG_DB_LANGUAGE__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_LANGUAGE__RELABELTO
| #define SEPG_DB_LANGUAGE__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_LANGUAGE__SETATTR
| #define SEPG_DB_LANGUAGE__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_PROCEDURE__CREATE
| #define SEPG_DB_PROCEDURE__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_PROCEDURE__DROP
| #define SEPG_DB_PROCEDURE__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_PROCEDURE__ENTRYPOINT
◆ SEPG_DB_PROCEDURE__EXECUTE
◆ SEPG_DB_PROCEDURE__GETATTR
| #define SEPG_DB_PROCEDURE__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_PROCEDURE__INSTALL
◆ SEPG_DB_PROCEDURE__RELABELFROM
| #define SEPG_DB_PROCEDURE__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_PROCEDURE__RELABELTO
| #define SEPG_DB_PROCEDURE__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_PROCEDURE__SETATTR
| #define SEPG_DB_PROCEDURE__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_SCHEMA__ADD_NAME
◆ SEPG_DB_SCHEMA__CREATE
| #define SEPG_DB_SCHEMA__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_SCHEMA__DROP
| #define SEPG_DB_SCHEMA__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_SCHEMA__GETATTR
| #define SEPG_DB_SCHEMA__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_SCHEMA__RELABELFROM
| #define SEPG_DB_SCHEMA__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_SCHEMA__RELABELTO
| #define SEPG_DB_SCHEMA__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_SCHEMA__REMOVE_NAME
◆ SEPG_DB_SCHEMA__SEARCH
◆ SEPG_DB_SCHEMA__SETATTR
| #define SEPG_DB_SCHEMA__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_SEQUENCE__CREATE
| #define SEPG_DB_SEQUENCE__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_SEQUENCE__DROP
| #define SEPG_DB_SEQUENCE__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_SEQUENCE__GET_VALUE
◆ SEPG_DB_SEQUENCE__GETATTR
| #define SEPG_DB_SEQUENCE__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_SEQUENCE__NEXT_VALUE
◆ SEPG_DB_SEQUENCE__RELABELFROM
| #define SEPG_DB_SEQUENCE__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_SEQUENCE__RELABELTO
| #define SEPG_DB_SEQUENCE__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_SEQUENCE__SET_VALUE
◆ SEPG_DB_SEQUENCE__SETATTR
| #define SEPG_DB_SEQUENCE__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_TABLE__CREATE
| #define SEPG_DB_TABLE__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_TABLE__DELETE
◆ SEPG_DB_TABLE__DROP
| #define SEPG_DB_TABLE__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_TABLE__GETATTR
| #define SEPG_DB_TABLE__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_TABLE__INSERT
◆ SEPG_DB_TABLE__LOCK
◆ SEPG_DB_TABLE__RELABELFROM
| #define SEPG_DB_TABLE__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_TABLE__RELABELTO
| #define SEPG_DB_TABLE__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_TABLE__SELECT
◆ SEPG_DB_TABLE__SETATTR
| #define SEPG_DB_TABLE__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_TABLE__TRUNCATE
◆ SEPG_DB_TABLE__UPDATE
◆ SEPG_DB_TUPLE__DELETE
| #define SEPG_DB_TUPLE__DELETE (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_TUPLE__INSERT
| #define SEPG_DB_TUPLE__INSERT (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_TUPLE__RELABELFROM
| #define SEPG_DB_TUPLE__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_TUPLE__RELABELTO
| #define SEPG_DB_TUPLE__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_TUPLE__SELECT
| #define SEPG_DB_TUPLE__SELECT (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_TUPLE__UPDATE
| #define SEPG_DB_TUPLE__UPDATE (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DB_VIEW__CREATE
| #define SEPG_DB_VIEW__CREATE (SEPG_DB_DATABASE__CREATE) |
◆ SEPG_DB_VIEW__DROP
| #define SEPG_DB_VIEW__DROP (SEPG_DB_DATABASE__DROP) |
◆ SEPG_DB_VIEW__EXPAND
◆ SEPG_DB_VIEW__GETATTR
| #define SEPG_DB_VIEW__GETATTR (SEPG_DB_DATABASE__GETATTR) |
◆ SEPG_DB_VIEW__RELABELFROM
| #define SEPG_DB_VIEW__RELABELFROM (SEPG_DB_DATABASE__RELABELFROM) |
◆ SEPG_DB_VIEW__RELABELTO
| #define SEPG_DB_VIEW__RELABELTO (SEPG_DB_DATABASE__RELABELTO) |
◆ SEPG_DB_VIEW__SETATTR
| #define SEPG_DB_VIEW__SETATTR (SEPG_DB_DATABASE__SETATTR) |
◆ SEPG_DIR__ADD_NAME
◆ SEPG_DIR__CREATE
| #define SEPG_DIR__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_DIR__GETATTR
| #define SEPG_DIR__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_DIR__READ
| #define SEPG_DIR__READ (SEPG_FILE__READ) |
◆ SEPG_DIR__REMOVE_NAME
◆ SEPG_DIR__RENAME
| #define SEPG_DIR__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_DIR__REPARENT
◆ SEPG_DIR__RMDIR
◆ SEPG_DIR__SEARCH
◆ SEPG_DIR__UNLINK
| #define SEPG_DIR__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_DIR__WRITE
| #define SEPG_DIR__WRITE (SEPG_FILE__WRITE) |
◆ SEPG_FIFO_FILE__CREATE
| #define SEPG_FIFO_FILE__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_FIFO_FILE__GETATTR
| #define SEPG_FIFO_FILE__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_FIFO_FILE__READ
| #define SEPG_FIFO_FILE__READ (SEPG_FILE__READ) |
◆ SEPG_FIFO_FILE__RENAME
| #define SEPG_FIFO_FILE__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_FIFO_FILE__UNLINK
| #define SEPG_FIFO_FILE__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_FIFO_FILE__WRITE
| #define SEPG_FIFO_FILE__WRITE (SEPG_FILE__WRITE) |
◆ SEPG_FILE__APPEND
◆ SEPG_FILE__CREATE
◆ SEPG_FILE__GETATTR
◆ SEPG_FILE__READ
◆ SEPG_FILE__RENAME
◆ SEPG_FILE__UNLINK
◆ SEPG_FILE__WRITE
◆ SEPG_LNK_FILE__CREATE
| #define SEPG_LNK_FILE__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_LNK_FILE__GETATTR
| #define SEPG_LNK_FILE__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_LNK_FILE__READ
| #define SEPG_LNK_FILE__READ (SEPG_FILE__READ) |
◆ SEPG_LNK_FILE__RENAME
| #define SEPG_LNK_FILE__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_LNK_FILE__UNLINK
| #define SEPG_LNK_FILE__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_LNK_FILE__WRITE
| #define SEPG_LNK_FILE__WRITE (SEPG_FILE__WRITE) |
◆ SEPG_PROCESS__DYNTRANSITION
◆ SEPG_PROCESS__SETCURRENT
◆ SEPG_PROCESS__TRANSITION
◆ SEPG_SOCK_FILE__CREATE
| #define SEPG_SOCK_FILE__CREATE (SEPG_FILE__CREATE) |
◆ SEPG_SOCK_FILE__GETATTR
| #define SEPG_SOCK_FILE__GETATTR (SEPG_FILE__GETATTR) |
◆ SEPG_SOCK_FILE__READ
| #define SEPG_SOCK_FILE__READ (SEPG_FILE__READ) |
◆ SEPG_SOCK_FILE__RENAME
| #define SEPG_SOCK_FILE__RENAME (SEPG_FILE__RENAME) |
◆ SEPG_SOCK_FILE__UNLINK
| #define SEPG_SOCK_FILE__UNLINK (SEPG_FILE__UNLINK) |
◆ SEPG_SOCK_FILE__WRITE
| #define SEPG_SOCK_FILE__WRITE (SEPG_FILE__WRITE) |
◆ SEPGSQL_AVC_NOAUDIT
◆ SEPGSQL_LABEL_TAG
◆ SEPGSQL_MODE_DEFAULT
◆ SEPGSQL_MODE_DISABLED
◆ SEPGSQL_MODE_INTERNAL
◆ SEPGSQL_MODE_PERMISSIVE
Function Documentation
◆ sepgsql_attribute_drop()
|
extern |
Definition at line 133 of file relation.c.
References attnum, fb(), get_rel_relkind(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_COLUMN, SEPG_DB_COLUMN__DROP, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_attribute_post_create()
|
extern |
Definition at line 43 of file relation.c.
References AccessShareLock, appendStringInfo(), attnum, BTEqualStrategyNumber, elog, ERROR, fb(), get_rel_relkind(), getObjectIdentity(), GETSTRUCT(), HeapTupleIsValid, initStringInfo(), Int16GetDatum(), NameStr, ObjectIdGetDatum(), pfree(), quote_identifier(), ScanKeyInit(), SEPG_CLASS_DB_COLUMN, SEPG_DB_COLUMN__CREATE, sepgsql_avc_check_perms_label(), sepgsql_compute_create(), sepgsql_get_client_label(), sepgsql_get_label(), SEPGSQL_LABEL_TAG, SetSecurityLabel(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_attribute_relabel()
|
extern |
Definition at line 165 of file relation.c.
References attnum, ereport, errcode(), errmsg, ERROR, fb(), get_rel_relkind(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_COLUMN, SEPG_DB_COLUMN__RELABELFROM, SEPG_DB_COLUMN__SETATTR, SEPG_DB_PROCEDURE__RELABELTO, sepgsql_avc_check_perms(), and sepgsql_avc_check_perms_label().
Referenced by sepgsql_object_relabel().
◆ sepgsql_attribute_setattr()
|
extern |
Definition at line 209 of file relation.c.
References attnum, fb(), get_rel_relkind(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_COLUMN, SEPG_DB_COLUMN__SETATTR, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_audit_log()
|
extern |
Definition at line 678 of file selinux.c.
References appendStringInfo(), appendStringInfoString(), Assert, av_name, buf, class_name, ereport, errmsg, fb(), i, initStringInfo(), LOG, selinux_catalog, and SEPG_CLASS_MAX.
Referenced by sepgsql_avc_check_perms_label().
◆ sepgsql_avc_check_perms()
|
extern |
Definition at line 420 of file uavc.c.
References fb(), GetSecurityLabel(), pfree(), sepgsql_avc_check_perms_label(), and SEPGSQL_LABEL_TAG.
Referenced by check_relation_privileges(), check_schema_perms(), sepgsql_attribute_drop(), sepgsql_attribute_relabel(), sepgsql_attribute_setattr(), sepgsql_database_drop(), sepgsql_database_relabel(), sepgsql_database_setattr(), sepgsql_fmgr_hook(), sepgsql_needs_fmgr_hook(), sepgsql_proc_drop(), sepgsql_proc_execute(), sepgsql_proc_post_create(), sepgsql_proc_relabel(), sepgsql_proc_setattr(), sepgsql_relation_drop(), sepgsql_relation_post_create(), sepgsql_relation_relabel(), sepgsql_relation_setattr(), sepgsql_relation_truncate(), sepgsql_schema_drop(), and sepgsql_schema_relabel().
◆ sepgsql_avc_check_perms_label()
|
extern |
Definition at line 337 of file uavc.c.
References avc_cache::allowed, avc_cache::auditallow, avc_cache::auditdeny, ereport, errcode(), errmsg, ERROR, fb(), avc_cache::permissive, result, avc_cache::scontext, sepgsql_audit_log(), sepgsql_avc_check_valid(), sepgsql_avc_lookup(), SEPGSQL_AVC_NOAUDIT, sepgsql_avc_unlabeled(), sepgsql_get_client_label(), sepgsql_get_debug_audit(), sepgsql_get_mode(), sepgsql_getenforce(), SEPGSQL_MODE_INTERNAL, avc_cache::tclass, avc_cache::tcontext, and avc_cache::tcontext_is_valid.
Referenced by sepgsql_attribute_post_create(), sepgsql_attribute_relabel(), sepgsql_avc_check_perms(), sepgsql_database_post_create(), sepgsql_database_relabel(), sepgsql_fmgr_hook(), sepgsql_proc_post_create(), sepgsql_proc_relabel(), sepgsql_relation_post_create(), sepgsql_relation_relabel(), sepgsql_schema_post_create(), sepgsql_schema_relabel(), and sepgsql_set_client_label().
◆ sepgsql_avc_init()
Definition at line 488 of file uavc.c.
References ALLOCSET_DEFAULT_SIZES, AllocSetContextCreate, AVC_DEF_THRESHOLD, avc_lru_hint, avc_mem_cxt, avc_num_caches, avc_slots, avc_threshold, ereport, errcode(), errmsg, ERROR, fb(), LOG, on_proc_exit(), sepgsql_avc_exit(), and TopMemoryContext.
Referenced by _PG_init().
◆ sepgsql_avc_trusted_proc()
Definition at line 445 of file uavc.c.
References fb(), GetSecurityLabel(), avc_cache::ncontext, SEPG_CLASS_DB_PROCEDURE, sepgsql_avc_check_valid(), sepgsql_avc_lookup(), sepgsql_avc_unlabeled(), sepgsql_get_client_label(), and SEPGSQL_LABEL_TAG.
Referenced by sepgsql_fmgr_hook(), and sepgsql_needs_fmgr_hook().
◆ sepgsql_compute_avd()
|
extern |
Definition at line 739 of file selinux.c.
References Assert, av_code, av_name, class_code, ereport, errcode(), errmsg, ERROR, fb(), i, selinux_catalog, and SEPG_CLASS_MAX.
Referenced by sepgsql_avc_compute().
◆ sepgsql_compute_create()
|
extern |
Definition at line 842 of file selinux.c.
References Assert, ereport, errcode(), errmsg, ERROR, fb(), PG_END_TRY, PG_FINALLY, PG_TRY, pstrdup(), result, selinux_catalog, and SEPG_CLASS_MAX.
Referenced by sepgsql_attribute_post_create(), sepgsql_avc_compute(), sepgsql_database_post_create(), sepgsql_proc_post_create(), sepgsql_relation_post_create(), and sepgsql_schema_post_create().
◆ sepgsql_database_drop()
Definition at line 132 of file database.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_DATABASE, SEPG_DB_DATABASE__DROP, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_database_post_create()
Definition at line 32 of file database.c.
References AccessShareLock, appendStringInfoString(), BTEqualStrategyNumber, elog, ERROR, fb(), Form_pg_database, get_database_oid(), GETSTRUCT(), HeapTupleIsValid, initStringInfo(), NameStr, ObjectIdGetDatum(), pfree(), quote_identifier(), resetStringInfo(), ScanKeyInit(), SEPG_CLASS_DB_DATABASE, SEPG_DB_DATABASE__CREATE, SEPG_DB_DATABASE__GETATTR, sepgsql_avc_check_perms_label(), sepgsql_compute_create(), sepgsql_get_client_label(), sepgsql_get_label(), SEPGSQL_LABEL_TAG, SetSecurityLabel(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_database_relabel()
Definition at line 186 of file database.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_DATABASE, SEPG_DB_DATABASE__RELABELFROM, SEPG_DB_DATABASE__RELABELTO, SEPG_DB_DATABASE__SETATTR, sepgsql_avc_check_perms(), and sepgsql_avc_check_perms_label().
Referenced by sepgsql_object_relabel().
◆ sepgsql_database_setattr()
Definition at line 159 of file database.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_DATABASE, SEPG_DB_DATABASE__SETATTR, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_dml_privileges()
|
extern |
Definition at line 282 of file dml.c.
References ACL_DELETE, ACL_INSERT, ACL_SELECT, ACL_UPDATE, bms_is_empty, check_relation_privileges(), fb(), find_all_inheritors(), fixup_inherited_columns(), lfirst_node, lfirst_oid, list_free(), list_make1_oid, NoLock, SEPG_DB_TABLE__DELETE, SEPG_DB_TABLE__INSERT, SEPG_DB_TABLE__LOCK, SEPG_DB_TABLE__SELECT, and SEPG_DB_TABLE__UPDATE.
Referenced by sepgsql_exec_check_perms().
◆ sepgsql_get_client_label()
Definition at line 79 of file label.c.
References Assert, client_label_committed, client_label_func, client_label_peer, client_label_pending, fb(), and llast.
Referenced by sepgsql_attribute_post_create(), sepgsql_avc_check_perms_label(), sepgsql_avc_trusted_proc(), sepgsql_database_post_create(), sepgsql_getcon(), sepgsql_proc_post_create(), sepgsql_relation_post_create(), sepgsql_schema_post_create(), and sepgsql_set_client_label().
◆ sepgsql_get_debug_audit()
Definition at line 77 of file hooks.c.
References sepgsql_debug_audit.
Referenced by sepgsql_avc_check_perms_label().
◆ sepgsql_get_label()
Definition at line 444 of file label.c.
References ObjectAddress::classId, ereport, errcode(), errmsg, ERROR, fb(), GetSecurityLabel(), label, PG_END_TRY, PG_FINALLY, PG_TRY, pstrdup(), and SEPGSQL_LABEL_TAG.
Referenced by sepgsql_attribute_post_create(), sepgsql_database_post_create(), sepgsql_proc_post_create(), sepgsql_relation_post_create(), and sepgsql_schema_post_create().
◆ sepgsql_get_mode()
Definition at line 625 of file selinux.c.
References sepgsql_mode.
Referenced by sepgsql_avc_check_perms_label().
◆ sepgsql_get_permissive()
Definition at line 66 of file hooks.c.
References sepgsql_permissive.
Referenced by sepgsql_client_auth().
◆ sepgsql_getenforce()
Definition at line 651 of file selinux.c.
References fb(), sepgsql_mode, and SEPGSQL_MODE_DEFAULT.
Referenced by check_relation_privileges(), sepgsql_avc_check_perms_label(), and sepgsql_utility_command().
◆ sepgsql_init_client_label()
Definition at line 403 of file label.c.
References client_label_peer, ClientAuthentication_hook, ereport, errcode(), errmsg, ERROR, fb(), fmgr_hook, needs_fmgr_hook, next_client_auth_hook, next_fmgr_hook, next_needs_fmgr_hook, RegisterSubXactCallback(), RegisterXactCallback(), sepgsql_client_auth(), sepgsql_fmgr_hook(), sepgsql_needs_fmgr_hook(), sepgsql_subxact_callback(), and sepgsql_xact_callback().
Referenced by _PG_init().
◆ sepgsql_is_enabled()
Definition at line 616 of file selinux.c.
References sepgsql_mode, and SEPGSQL_MODE_DISABLED.
Referenced by sepgsql_getcon(), sepgsql_mcstrans_in(), sepgsql_mcstrans_out(), and sepgsql_restorecon().
◆ sepgsql_object_relabel()
|
extern |
Definition at line 481 of file label.c.
References ObjectAddress::classId, ereport, errcode(), errmsg, ERROR, fb(), getObjectTypeDescription(), ObjectAddress::objectId, ObjectAddress::objectSubId, sepgsql_attribute_relabel(), sepgsql_database_relabel(), sepgsql_proc_relabel(), sepgsql_relation_relabel(), and sepgsql_schema_relabel().
Referenced by _PG_init(), and exec_object_restorecon().
◆ sepgsql_proc_drop()
Definition at line 155 of file proc.c.
References ObjectAddress::classId, fb(), get_func_namespace(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_PROCEDURE, SEPG_CLASS_DB_SCHEMA, SEPG_DB_PROCEDURE__DROP, SEPG_DB_SCHEMA__REMOVE_NAME, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_proc_execute()
Definition at line 315 of file proc.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_PROCEDURE, SEPG_DB_PROCEDURE__EXECUTE, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_proc_post_create()
Definition at line 37 of file proc.c.
References AccessShareLock, appendStringInfo(), appendStringInfoChar(), appendStringInfoString(), BTEqualStrategyNumber, elog, ERROR, fb(), Form_pg_proc, get_namespace_name(), getObjectIdentity(), GETSTRUCT(), HeapTupleIsValid, i, initStringInfo(), NameStr, ObjectIdGetDatum(), pfree(), quote_qualified_identifier(), ScanKeyInit(), SEPG_CLASS_DB_PROCEDURE, SEPG_CLASS_DB_SCHEMA, SEPG_DB_PROCEDURE__CREATE, SEPG_DB_PROCEDURE__INSTALL, SEPG_DB_SCHEMA__ADD_NAME, sepgsql_avc_check_perms(), sepgsql_avc_check_perms_label(), sepgsql_compute_create(), sepgsql_get_client_label(), sepgsql_get_label(), SEPGSQL_LABEL_TAG, SetSecurityLabel(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_proc_relabel()
Definition at line 198 of file proc.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_PROCEDURE, SEPG_DB_PROCEDURE__RELABELFROM, SEPG_DB_PROCEDURE__RELABELTO, SEPG_DB_PROCEDURE__SETATTR, sepgsql_avc_check_perms(), and sepgsql_avc_check_perms_label().
Referenced by sepgsql_object_relabel().
◆ sepgsql_proc_setattr()
Definition at line 235 of file proc.c.
References AccessShareLock, BTEqualStrategyNumber, elog, ERROR, fb(), Form_pg_proc, getObjectIdentity(), GETSTRUCT(), HeapTupleIsValid, NameStr, ObjectIdGetDatum(), pfree(), ReleaseSysCache(), ScanKeyInit(), SearchSysCache1(), SEPG_CLASS_DB_PROCEDURE, SEPG_DB_PROCEDURE__INSTALL, SEPG_DB_PROCEDURE__SETATTR, sepgsql_avc_check_perms(), sepgsql_schema_add_name(), sepgsql_schema_remove_name(), sepgsql_schema_rename(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_relation_drop()
Definition at line 416 of file relation.c.
References fb(), get_rel_namespace(), get_rel_relkind(), getObjectIdentity(), GETSTRUCT(), i, ObjectIdGetDatum(), pfree(), ReleaseCatCacheList(), SearchSysCacheList1, SEPG_CLASS_DB_COLUMN, SEPG_CLASS_DB_SCHEMA, SEPG_CLASS_DB_SEQUENCE, SEPG_CLASS_DB_TABLE, SEPG_CLASS_DB_VIEW, SEPG_DB_COLUMN__DROP, SEPG_DB_SCHEMA__REMOVE_NAME, SEPG_DB_TABLE__DROP, sepgsql_avc_check_perms(), and sepgsql_index_modify().
Referenced by sepgsql_object_access().
◆ sepgsql_relation_post_create()
Definition at line 240 of file relation.c.
References AccessShareLock, appendStringInfo(), BTEqualStrategyNumber, elog, ERROR, fb(), get_namespace_name(), getObjectIdentity(), GETSTRUCT(), HeapTupleIsValid, initStringInfo(), NameStr, ObjectIdGetDatum(), pfree(), quote_identifier(), resetStringInfo(), ScanKeyInit(), SEPG_CLASS_DB_COLUMN, SEPG_CLASS_DB_SCHEMA, SEPG_CLASS_DB_SEQUENCE, SEPG_CLASS_DB_TABLE, SEPG_CLASS_DB_VIEW, SEPG_DB_COLUMN__CREATE, SEPG_DB_DATABASE__CREATE, SEPG_DB_SCHEMA__ADD_NAME, sepgsql_avc_check_perms(), sepgsql_avc_check_perms_label(), sepgsql_compute_create(), sepgsql_get_client_label(), sepgsql_get_label(), sepgsql_index_modify(), SEPGSQL_LABEL_TAG, SetSecurityLabel(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_relation_relabel()
Definition at line 564 of file relation.c.
References ereport, errcode(), errmsg, ERROR, fb(), get_rel_relkind(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_SEQUENCE, SEPG_CLASS_DB_TABLE, SEPG_CLASS_DB_VIEW, SEPG_DB_TABLE__RELABELFROM, SEPG_DB_TABLE__RELABELTO, SEPG_DB_TABLE__SETATTR, sepgsql_avc_check_perms(), and sepgsql_avc_check_perms_label().
Referenced by sepgsql_object_relabel().
◆ sepgsql_relation_setattr()
Definition at line 615 of file relation.c.
References AccessShareLock, BTEqualStrategyNumber, elog, ERROR, fb(), get_rel_relkind(), getObjectIdentity(), GETSTRUCT(), HeapTupleIsValid, NameStr, ObjectIdGetDatum(), pfree(), ReleaseSysCache(), ScanKeyInit(), SearchSysCache1(), SEPG_CLASS_DB_SEQUENCE, SEPG_CLASS_DB_TABLE, SEPG_CLASS_DB_VIEW, SEPG_DB_TABLE__SETATTR, sepgsql_avc_check_perms(), sepgsql_index_modify(), sepgsql_schema_add_name(), sepgsql_schema_remove_name(), sepgsql_schema_rename(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access(), and sepgsql_relation_setattr_extra().
◆ sepgsql_relation_truncate()
Definition at line 524 of file relation.c.
References fb(), get_rel_relkind(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_TABLE, SEPG_DB_TABLE__TRUNCATE, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_schema_add_name()
Definition at line 217 of file schema.c.
References check_schema_perms(), fb(), and SEPG_DB_SCHEMA__ADD_NAME.
Referenced by sepgsql_proc_setattr(), and sepgsql_relation_setattr().
◆ sepgsql_schema_drop()
Definition at line 114 of file schema.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_SCHEMA, SEPG_DB_SCHEMA__DROP, and sepgsql_avc_check_perms().
Referenced by sepgsql_object_access().
◆ sepgsql_schema_post_create()
Definition at line 36 of file schema.c.
References AccessShareLock, appendStringInfoString(), BTEqualStrategyNumber, elog, ERROR, fb(), Form_pg_namespace, GETSTRUCT(), HeapTupleIsValid, initStringInfo(), MyDatabaseId, NameStr, ObjectIdGetDatum(), pfree(), quote_identifier(), ScanKeyInit(), SEPG_CLASS_DB_SCHEMA, SEPG_DB_SCHEMA__CREATE, sepgsql_avc_check_perms_label(), sepgsql_compute_create(), sepgsql_get_client_label(), sepgsql_get_label(), SEPGSQL_LABEL_TAG, SetSecurityLabel(), SnapshotSelf, systable_beginscan(), systable_endscan(), systable_getnext(), table_close(), and table_open().
Referenced by sepgsql_object_access().
◆ sepgsql_schema_relabel()
Definition at line 142 of file schema.c.
References ObjectAddress::classId, fb(), getObjectIdentity(), pfree(), SEPG_CLASS_DB_SCHEMA, SEPG_DB_SCHEMA__RELABELFROM, SEPG_DB_SCHEMA__RELABELTO, SEPG_DB_SCHEMA__SETATTR, sepgsql_avc_check_perms(), and sepgsql_avc_check_perms_label().
Referenced by sepgsql_object_relabel().
◆ sepgsql_schema_remove_name()
Definition at line 223 of file schema.c.
References check_schema_perms(), fb(), and SEPG_DB_SCHEMA__REMOVE_NAME.
Referenced by sepgsql_proc_setattr(), and sepgsql_relation_setattr().
◆ sepgsql_schema_rename()
Definition at line 229 of file schema.c.
References check_schema_perms(), fb(), SEPG_DB_SCHEMA__ADD_NAME, and SEPG_DB_SCHEMA__REMOVE_NAME.
Referenced by sepgsql_proc_setattr(), and sepgsql_relation_setattr().
◆ sepgsql_schema_search()
Definition at line 209 of file schema.c.
References check_schema_perms(), fb(), and SEPG_DB_SCHEMA__SEARCH.
Referenced by sepgsql_object_access().
◆ sepgsql_schema_setattr()
Definition at line 202 of file schema.c.
References check_schema_perms(), fb(), and SEPG_DB_SCHEMA__SETATTR.
Referenced by sepgsql_object_access().
◆ sepgsql_set_mode()
Definition at line 634 of file selinux.c.
References fb(), and sepgsql_mode.
Referenced by _PG_init(), and sepgsql_client_auth().