#include "postgres.h"#include "access/htup.h"#include "access/htup_details.h"#include "access/transam.h"#include "catalog/namespace.h"#include "catalog/pg_class.h"#include "miscadmin.h"#include "utils/acl.h"#include "utils/fmgrprotos.h"#include "utils/lsyscache.h"#include "utils/rls.h"#include "utils/syscache.h"#include "utils/varlena.h"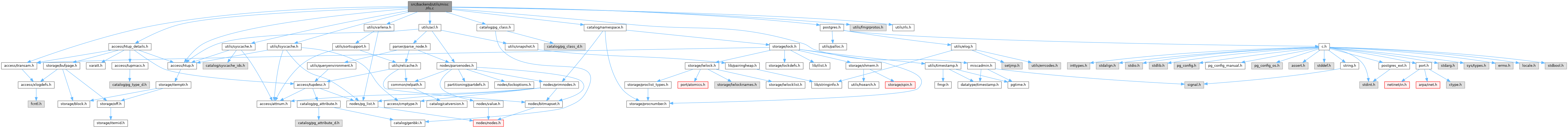
Go to the source code of this file.
Functions | |
| int | check_enable_rls (Oid relid, Oid checkAsUser, bool noError) |
| Datum | row_security_active (PG_FUNCTION_ARGS) |
| Datum | row_security_active_name (PG_FUNCTION_ARGS) |
Function Documentation
◆ check_enable_rls()
Definition at line 52 of file rls.c.
References ereport, errcode(), errhint(), errmsg, ERROR, fb(), FirstNormalObjectId, get_rel_name(), GETSTRUCT(), GetUserId(), has_bypassrls_privilege(), HeapTupleIsValid, InNoForceRLSOperation(), object_ownercheck(), ObjectIdGetDatum(), OidIsValid, ReleaseSysCache(), RLS_ENABLED, RLS_NONE, RLS_NONE_ENV, row_security, and SearchSysCache1().
Referenced by BuildIndexValueDescription(), DoCopy(), ExecBuildSlotPartitionKeyDescription(), ExecBuildSlotValueDescription(), get_row_security_policies(), intorel_startup(), LogicalRepSyncTableStart(), ri_ReportViolation(), row_security_active(), row_security_active_name(), and TargetPrivilegesCheck().
◆ row_security_active()
| Datum row_security_active | ( | PG_FUNCTION_ARGS | ) |
Definition at line 142 of file rls.c.
References check_enable_rls(), fb(), InvalidOid, PG_GETARG_OID, PG_RETURN_BOOL, and RLS_ENABLED.
◆ row_security_active_name()
| Datum row_security_active_name | ( | PG_FUNCTION_ARGS | ) |
Definition at line 153 of file rls.c.
References check_enable_rls(), fb(), InvalidOid, makeRangeVarFromNameList(), NoLock, PG_GETARG_TEXT_PP, PG_RETURN_BOOL, RangeVarGetRelid, RLS_ENABLED, and textToQualifiedNameList().