#include "catalog/objectaddress.h"#include "libpq/crypt.h"#include "nodes/parsenodes.h"#include "parser/parse_node.h"#include "utils/guc.h"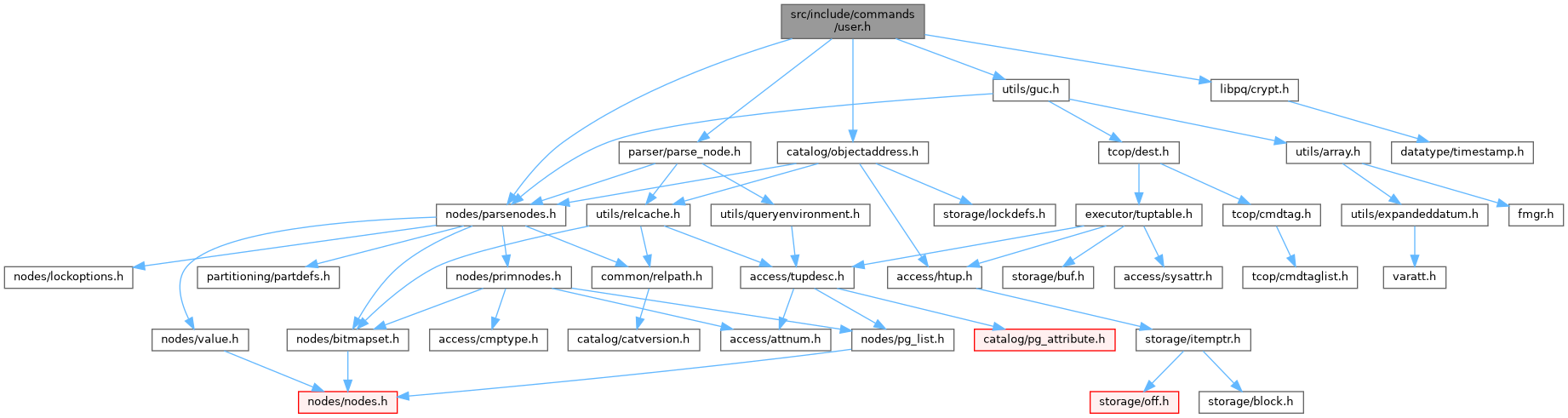
Go to the source code of this file.
Typedefs | |
| typedef void(* | check_password_hook_type) (const char *username, const char *shadow_pass, PasswordType password_type, Datum validuntil_time, bool validuntil_null) |
Functions | |
| Oid | CreateRole (ParseState *pstate, CreateRoleStmt *stmt) |
| Oid | AlterRole (ParseState *pstate, AlterRoleStmt *stmt) |
| Oid | AlterRoleSet (AlterRoleSetStmt *stmt) |
| void | DropRole (DropRoleStmt *stmt) |
| void | GrantRole (ParseState *pstate, GrantRoleStmt *stmt) |
| ObjectAddress | RenameRole (const char *oldname, const char *newname) |
| void | DropOwnedObjects (DropOwnedStmt *stmt) |
| void | ReassignOwnedObjects (ReassignOwnedStmt *stmt) |
| List * | roleSpecsToIds (List *memberNames) |
| bool | check_createrole_self_grant (char **newval, void **extra, GucSource source) |
| void | assign_createrole_self_grant (const char *newval, void *extra) |
Variables | |
| PGDLLIMPORT int | Password_encryption |
| PGDLLIMPORT char * | createrole_self_grant |
| PGDLLIMPORT check_password_hook_type | check_password_hook |
Typedef Documentation
◆ check_password_hook_type
| typedef void(* check_password_hook_type) (const char *username, const char *shadow_pass, PasswordType password_type, Datum validuntil_time, bool validuntil_null) |
Function Documentation
◆ AlterRole()
|
extern |
Definition at line 626 of file user.c.
References _, AddRoleMems(), BoolGetDatum(), boolVal, CatalogTupleUpdate(), check_password_hook, check_rolespec_name(), CommandCounterIncrement(), CStringGetDatum(), CStringGetTextDatum, DelRoleMems(), DirectFunctionCall3, DROP_RESTRICT, elog, encrypt_password(), ereport, errcode(), errdetail(), errmsg, ERROR, errorConflictingDefElem(), fb(), Form_pg_authid, get_password_type(), get_rolespec_tuple(), GETSTRUCT(), GetUserId(), has_bypassrls_privilege(), has_rolreplication(), have_createdb_privilege(), have_createrole_privilege(), heap_freetuple(), heap_modify_tuple(), InitGrantRoleOptions(), Int32GetDatum(), intVal, InvalidOid, InvokeObjectPostAlterHook, is_admin_of_role(), lfirst, NameStr, NoLock, NOTICE, ObjectIdGetDatum(), password, Password_encryption, plain_crypt_verify(), pstrdup(), RelationGetDescr, ReleaseSysCache(), roleSpecsToIds(), RowExclusiveLock, STATUS_OK, stmt, strVal, superuser(), SysCacheGetAttr(), HeapTupleData::t_self, table_close(), table_open(), and timestamptz_in().
Referenced by standard_ProcessUtility().
◆ AlterRoleSet()
|
extern |
Definition at line 1007 of file user.c.
References _, aclcheck_error(), ACLCHECK_NOT_OWNER, AlterSetting(), check_rolespec_name(), ereport, errcode(), errdetail(), errmsg, ERROR, fb(), Form_pg_authid, get_database_oid(), get_rolespec_tuple(), GETSTRUCT(), GetUserId(), have_createrole_privilege(), InvalidOid, is_admin_of_role(), NameStr, OBJECT_DATABASE, object_ownercheck(), ReleaseSysCache(), shdepLockAndCheckObject(), stmt, and superuser().
Referenced by standard_ProcessUtility().
◆ assign_createrole_self_grant()
Definition at line 2583 of file user.c.
References GrantRoleOptions::admin, createrole_self_grant_enabled, createrole_self_grant_options, GRANT_ROLE_SPECIFIED_ADMIN, GRANT_ROLE_SPECIFIED_INHERIT, GRANT_ROLE_SPECIFIED_SET, GrantRoleOptions::inherit, GrantRoleOptions::set, and GrantRoleOptions::specified.
◆ check_createrole_self_grant()
Definition at line 2530 of file user.c.
References fb(), GRANT_ROLE_SPECIFIED_INHERIT, GRANT_ROLE_SPECIFIED_SET, GUC_check_errdetail, guc_malloc(), lfirst, list_free(), LOG, newval, pfree(), pg_strcasecmp(), pstrdup(), result, and SplitIdentifierString().
◆ CreateRole()
|
extern |
Definition at line 133 of file user.c.
References AddRoleMems(), GrantRoleOptions::admin, binary_upgrade_next_pg_authid_oid, BoolGetDatum(), boolVal, CatalogTupleInsert(), check_password_hook, check_role_membership_authorization(), CommandCounterIncrement(), createdb(), createrole_self_grant_enabled, createrole_self_grant_options, CStringGetDatum(), CStringGetTextDatum, DirectFunctionCall1, DirectFunctionCall3, elog, encrypt_password(), ereport, errcode(), ERRCODE_DUPLICATE_OBJECT, errdetail(), errmsg, ERROR, errorConflictingDefElem(), fb(), Form_pg_authid, get_password_type(), get_role_oid(), get_rolespec_tuple(), GetNewOidWithIndex(), GETSTRUCT(), GetUserId(), GRANT_ROLE_SPECIFIED_ADMIN, GRANT_ROLE_SPECIFIED_INHERIT, GRANT_ROLE_SPECIFIED_SET, has_bypassrls_privilege(), has_createrole_privilege(), has_rolreplication(), have_createdb_privilege(), heap_form_tuple(), InitGrantRoleOptions(), Int32GetDatum(), intVal, InvalidOid, InvokeObjectPostCreateHook, IsBinaryUpgrade, IsReservedName(), lfirst, list_make1, list_make1_oid, makeNode, namein(), NameStr, NIL, NoLock, NOTICE, ObjectIdGetDatum(), OidIsValid, password, Password_encryption, plain_crypt_verify(), RelationGetDescr, ReleaseSysCache(), ROLESPEC_CSTRING, ROLESPEC_CURRENT_ROLE, roleSpecsToIds(), ROLESTMT_GROUP, ROLESTMT_ROLE, ROLESTMT_USER, RowExclusiveLock, GrantRoleOptions::specified, STATUS_OK, stmt, strVal, superuser(), superuser_arg(), table_close(), table_open(), timestamptz_in(), and WARNING.
Referenced by standard_ProcessUtility().
◆ DropOwnedObjects()
|
extern |
Definition at line 1596 of file user.c.
References ereport, errcode(), errdetail(), errmsg, ERROR, fb(), GetUserId(), GetUserNameFromId(), has_privs_of_role(), lfirst_oid, roleSpecsToIds(), shdepDropOwned(), and stmt.
Referenced by ProcessUtilitySlow().
◆ DropRole()
|
extern |
Definition at line 1097 of file user.c.
References AccessExclusiveLock, BTEqualStrategyNumber, CatalogTupleDelete(), checkSharedDependencies(), CommandCounterIncrement(), DeleteSharedComments(), deleteSharedDependencyRecordsFor(), DeleteSharedSecurityLabel(), DropSetting(), elog, ereport, errcode(), errdetail(), errdetail_internal(), errdetail_log(), errmsg, ERROR, fb(), Form_pg_auth_members, Form_pg_authid, GetOuterUserId(), GetSessionUserId(), GETSTRUCT(), GetUserId(), have_createrole_privilege(), HeapTupleIsValid, InvalidOid, InvokeObjectDropHook, is_admin_of_role(), lfirst, lfirst_oid, list_append_unique_oid(), LockSharedObject(), NameStr, NIL, NoLock, NOTICE, ObjectIdGetDatum(), PointerGetDatum, ReleaseSysCache(), ROLESPEC_CSTRING, RowExclusiveLock, ScanKeyInit(), SearchSysCache1(), stmt, superuser(), systable_beginscan(), systable_endscan(), systable_getnext(), HeapTupleData::t_self, table_close(), and table_open().
Referenced by standard_ProcessUtility().
◆ GrantRole()
|
extern |
Definition at line 1493 of file user.c.
References AccessShareLock, AddRoleMems(), GrantRoleOptions::admin, check_role_membership_authorization(), AccessPriv::cols, defGetString(), DefElem::defname, DelRoleMems(), ereport, errcode(), errmsg, ERROR, fb(), get_role_oid(), get_rolespec_oid(), GetUserId(), GRANT_ROLE_SPECIFIED_ADMIN, GRANT_ROLE_SPECIFIED_INHERIT, GRANT_ROLE_SPECIFIED_SET, GrantRoleOptions::inherit, InitGrantRoleOptions(), InvalidOid, lfirst, DefElem::location, NIL, NoLock, parse_bool(), parser_errposition(), AccessPriv::priv_name, roleSpecsToIds(), GrantRoleOptions::set, GrantRoleOptions::specified, stmt, table_close(), and table_open().
Referenced by standard_ProcessUtility().
◆ ReassignOwnedObjects()
|
extern |
Definition at line 1624 of file user.c.
References ereport, errcode(), errdetail(), errmsg, ERROR, fb(), get_rolespec_oid(), GetUserId(), GetUserNameFromId(), has_privs_of_role(), lfirst_oid, roleSpecsToIds(), shdepReassignOwned(), and stmt.
Referenced by standard_ProcessUtility().
◆ RenameRole()
|
extern |
Definition at line 1341 of file user.c.
References CatalogTupleUpdate(), CStringGetDatum(), DirectFunctionCall1, elog, ereport, errcode(), ERRCODE_DUPLICATE_OBJECT, errdetail(), errmsg, ERROR, fb(), Form_pg_authid, get_password_type(), GetOuterUserId(), GetSessionUserId(), GETSTRUCT(), GetUserId(), have_createrole_privilege(), heap_getattr(), heap_modify_tuple(), HeapTupleIsValid, i, InvokeObjectPostAlterHook, is_admin_of_role(), IsReservedName(), namein(), NameStr, NoLock, NOTICE, ObjectAddressSet, PASSWORD_TYPE_MD5, RelationGetDescr, ReleaseSysCache(), RowExclusiveLock, SearchSysCache1(), SearchSysCacheExists1, superuser(), HeapTupleData::t_self, table_close(), table_open(), TextDatumGetCString, and WARNING.
Referenced by ExecRenameStmt().
◆ roleSpecsToIds()
Definition at line 1665 of file user.c.
References fb(), get_rolespec_oid(), lappend_oid(), lfirst_node, NIL, and result.
Referenced by AlterRole(), AlterTableMoveAll(), CreateRole(), DropOwnedObjects(), GrantRole(), and ReassignOwnedObjects().
Variable Documentation
◆ check_password_hook
|
extern |
Definition at line 92 of file user.c.
Referenced by _PG_init(), AlterRole(), and CreateRole().
◆ createrole_self_grant
|
extern |
◆ Password_encryption
|
extern |
Definition at line 86 of file user.c.
Referenced by AlterRole(), CheckPWChallengeAuth(), and CreateRole().